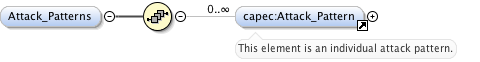
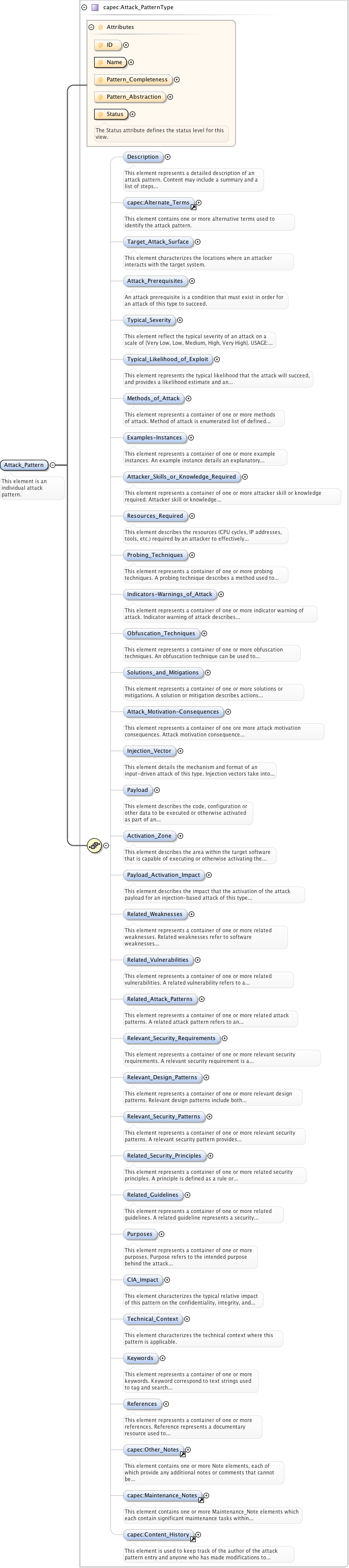
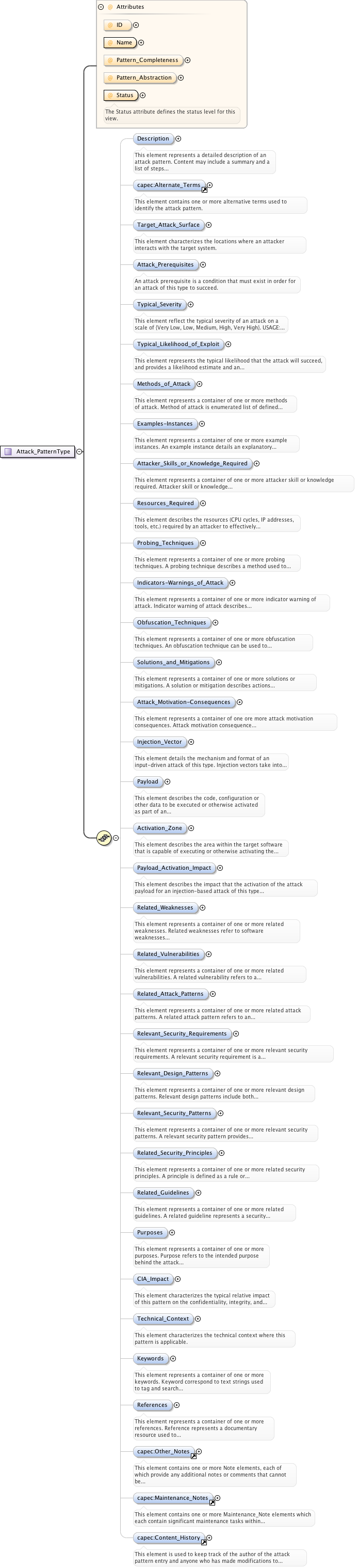
<xs:complexType name="Attack_PatternType">
<xs:sequence>
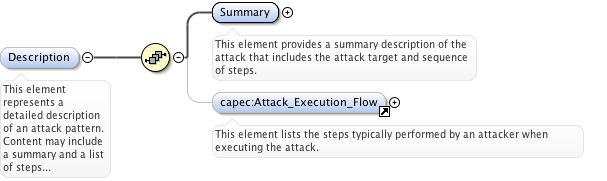
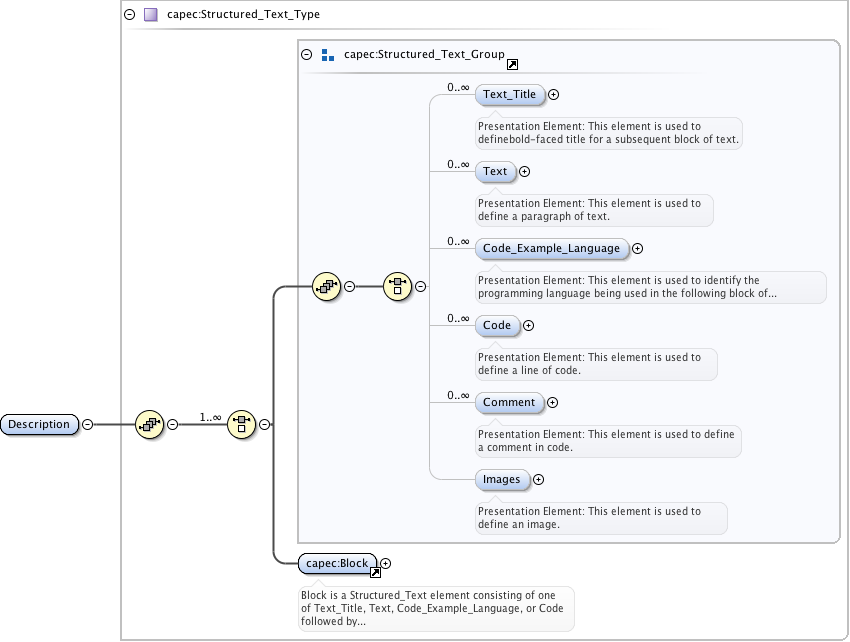
<xs:element name="Description" minOccurs="0">
<xs:annotation>
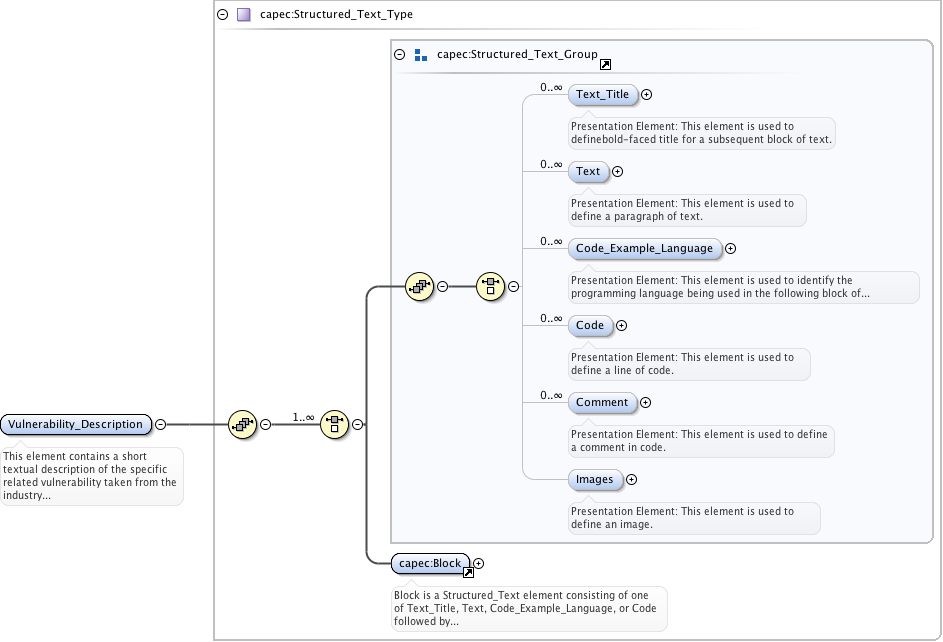
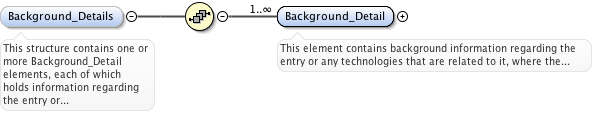
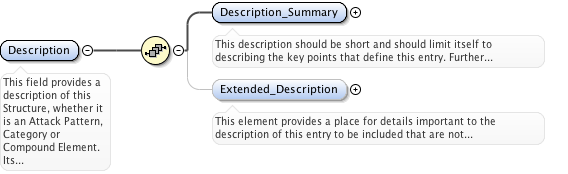
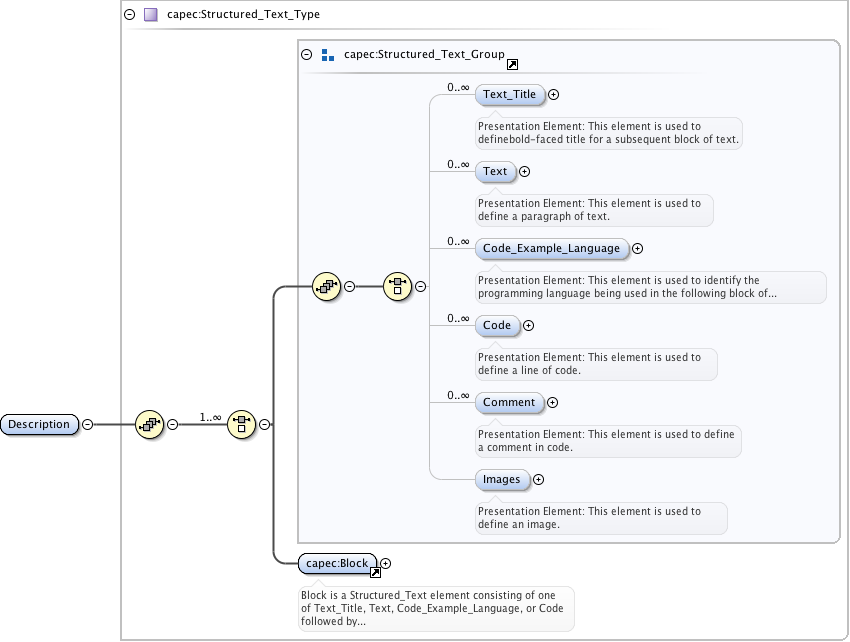
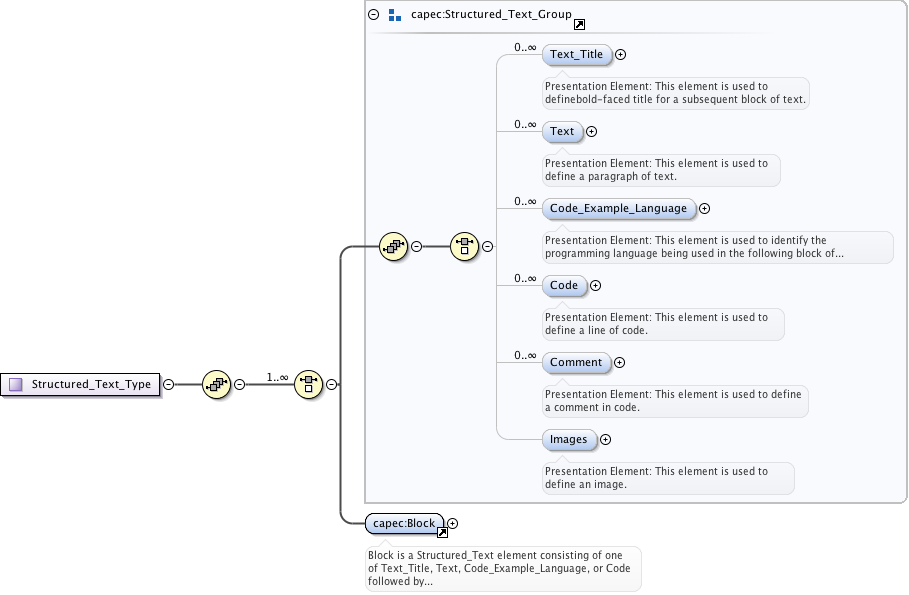
<xs:documentation>This element represents a detailed description of an attack pattern. Content may include a summary and a list of steps taken by the attacker. USAGE: This element can be used to capture a range of descriptive information. Comprehensive descriptions might include attack trees, exploit graphs, etc., to more clearly elaborate this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
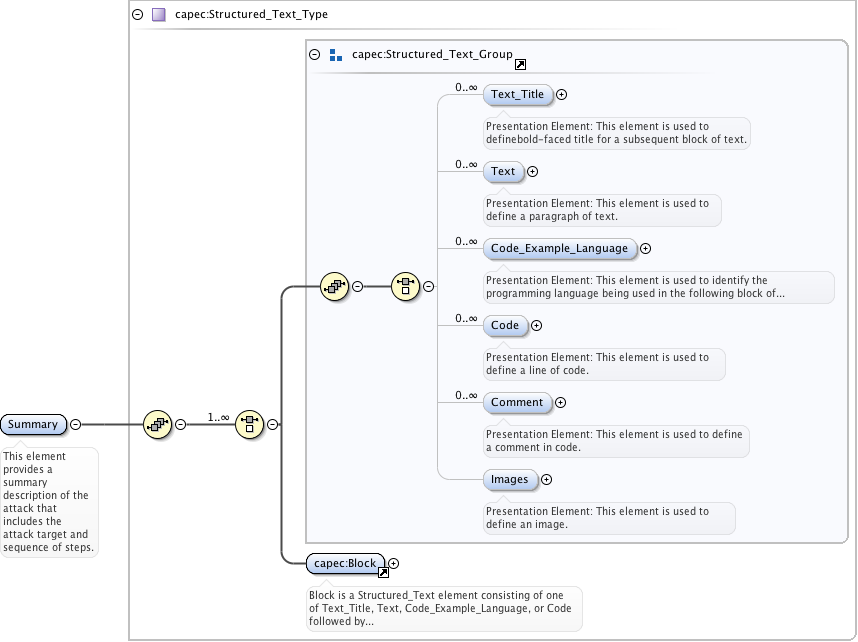
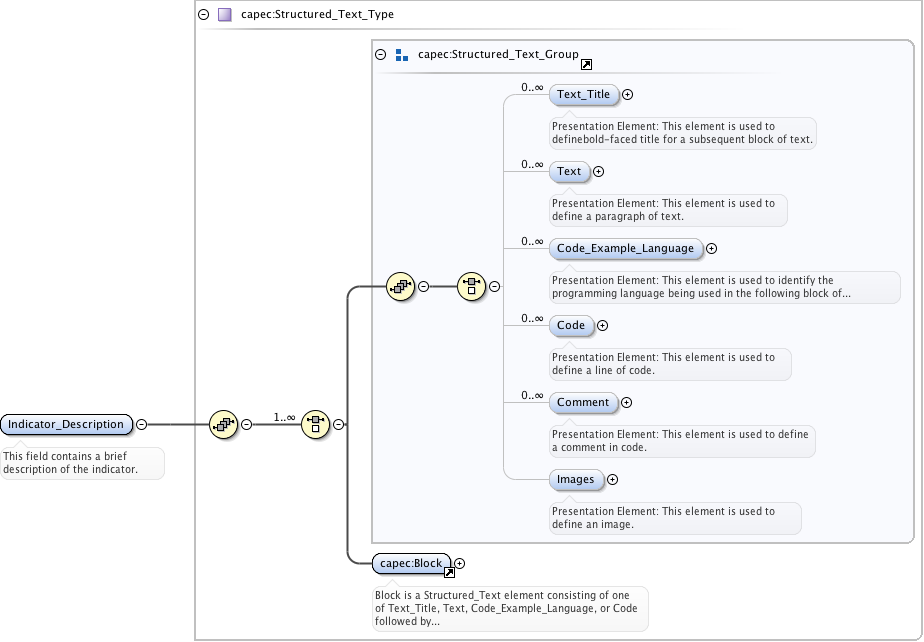
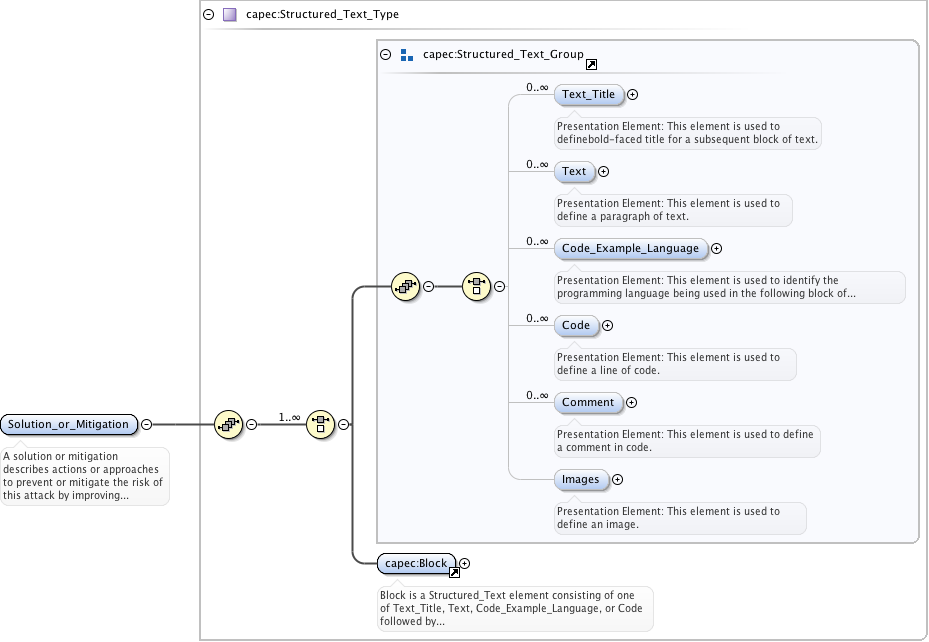
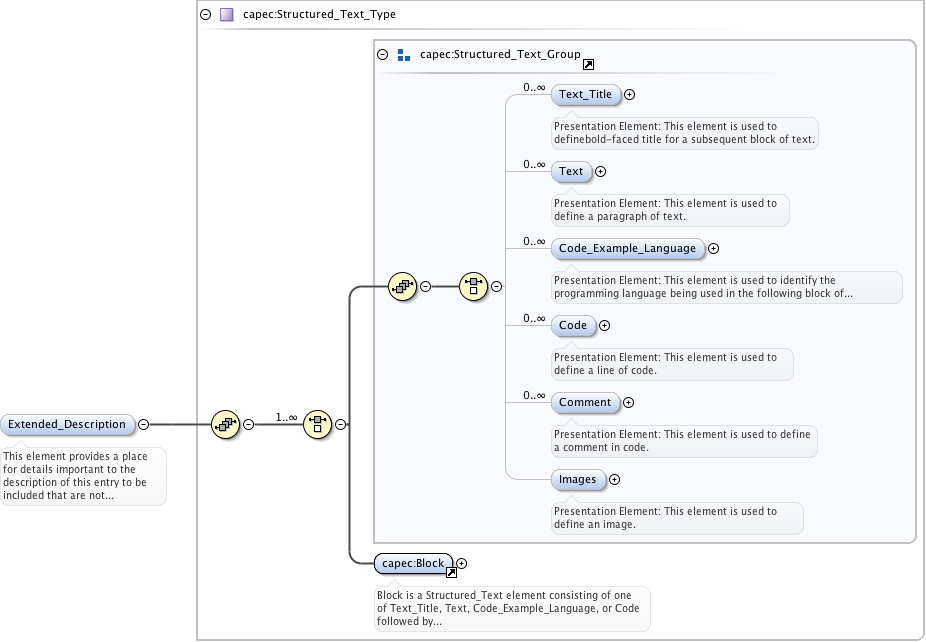
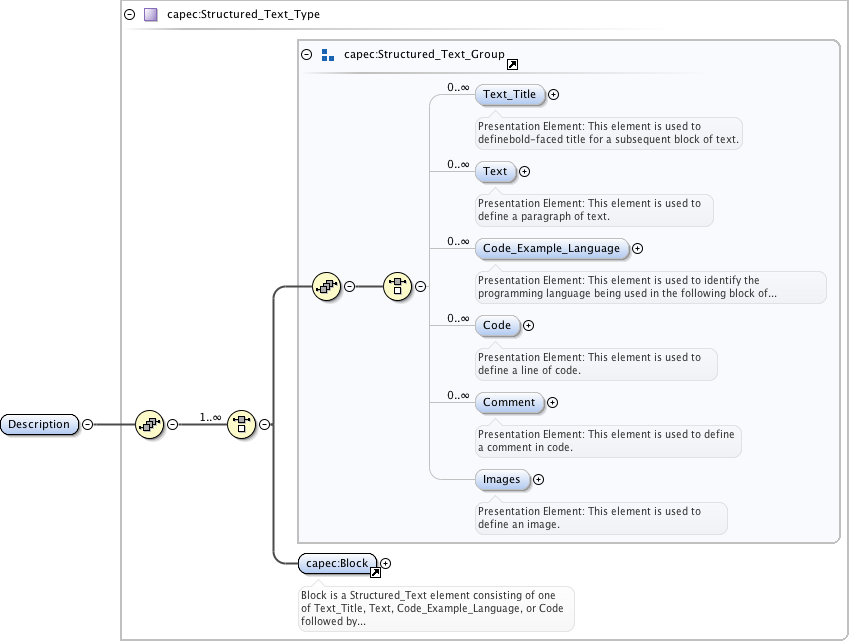
<xs:element name="Summary" type="capec:Structured_Text_Type">
<xs:annotation>
<xs:documentation>This element provides a summary description of the attack that includes the attack target and sequence of steps.</xs:documentation>
</xs:annotation>
</xs:element>
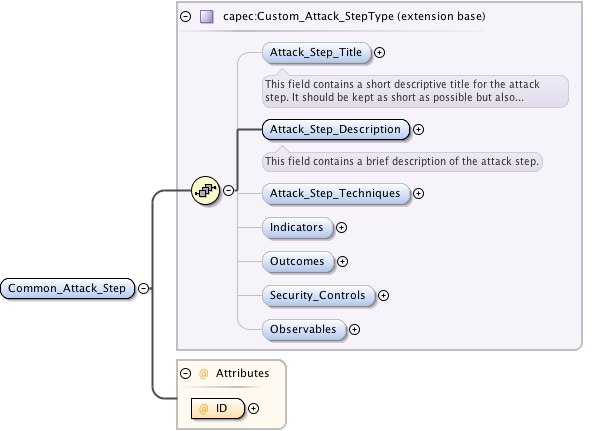
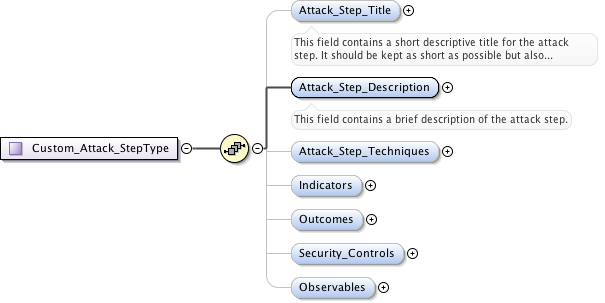
<xs:element ref="capec:Attack_Execution_Flow" minOccurs="0">
<xs:annotation>
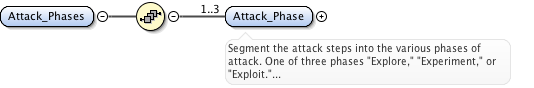
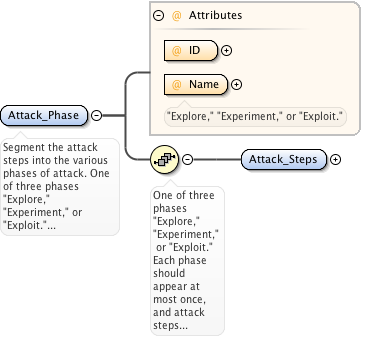
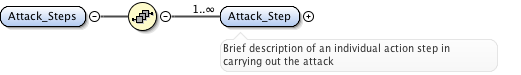
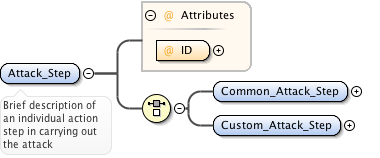
<xs:documentation>This element lists the steps typically performed by an attacker when executing the attack.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
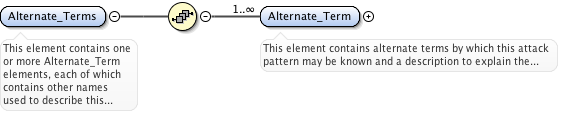
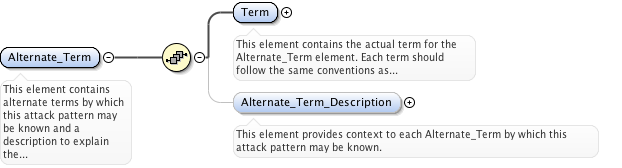
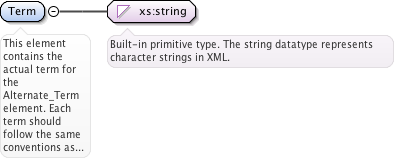
<xs:element ref="capec:Alternate_Terms" minOccurs="0">
<xs:annotation>
<xs:documentation>This element contains one or more alternative terms used to identify the attack pattern.</xs:documentation>
</xs:annotation>
</xs:element>
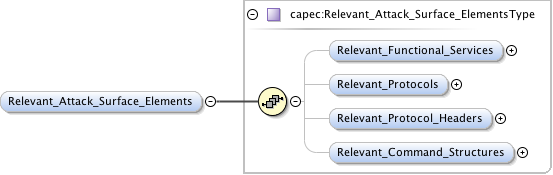
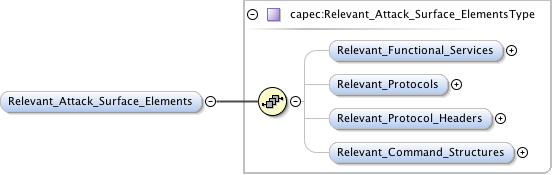
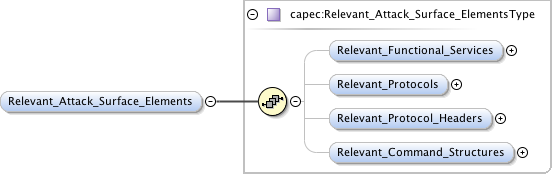
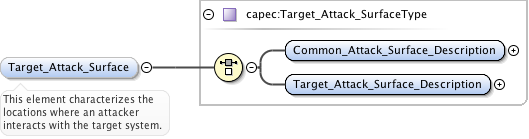
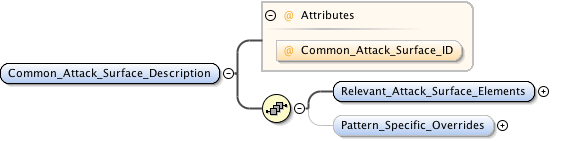
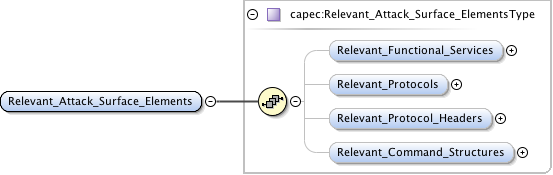
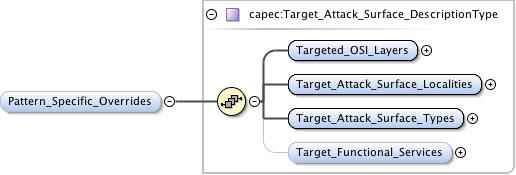
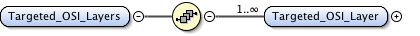
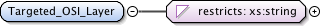
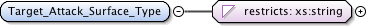
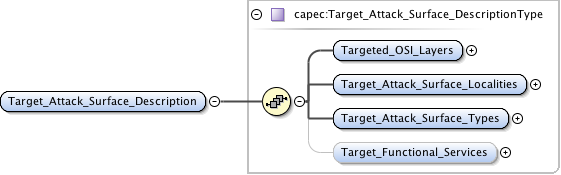
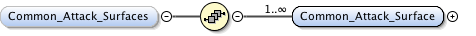
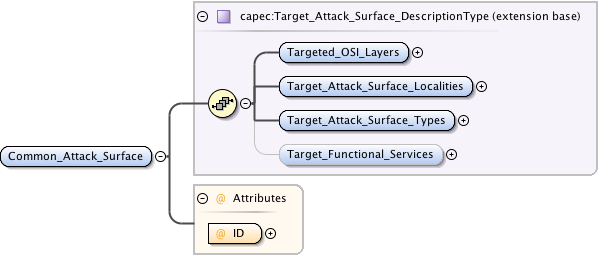
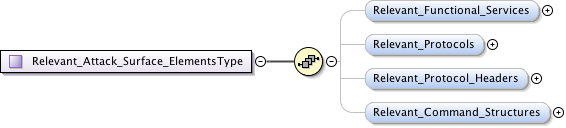
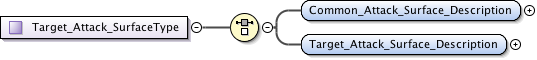
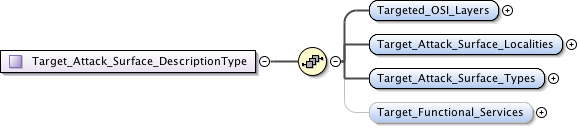
<xs:element name="Target_Attack_Surface" type="capec:Target_Attack_SurfaceType" minOccurs="0">
<xs:annotation>
<xs:documentation>This element characterizes the locations where an attacker interacts with the target system.</xs:documentation>
</xs:annotation>
</xs:element>
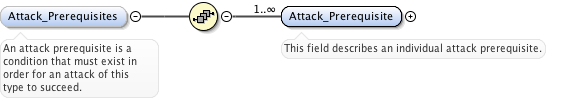
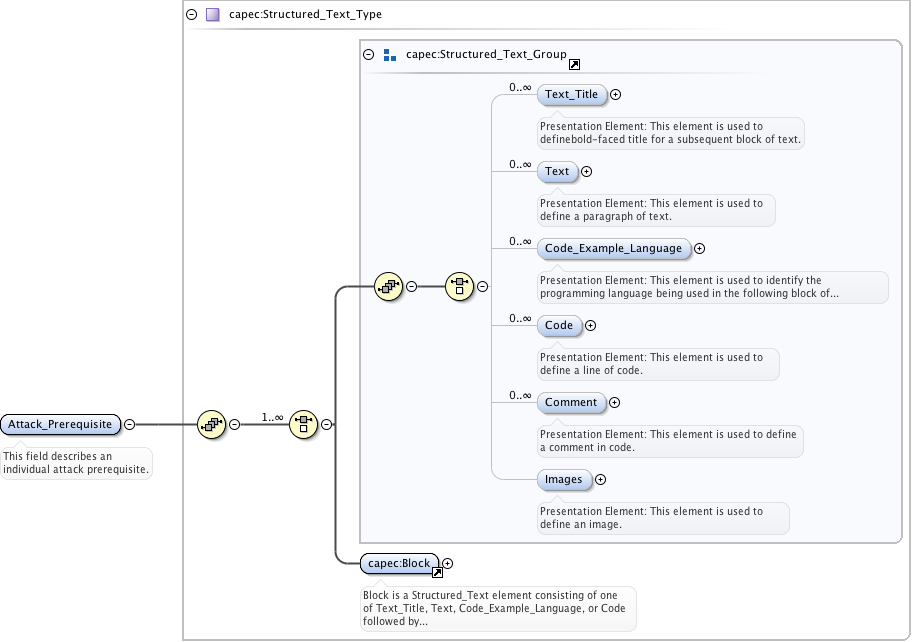
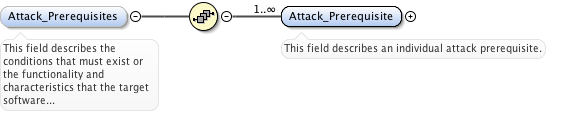
<xs:element name="Attack_Prerequisites" minOccurs="0">
<xs:annotation>
<xs:documentation>An attack prerequisite is a condition that must exist in order for an attack of this type to succeed.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
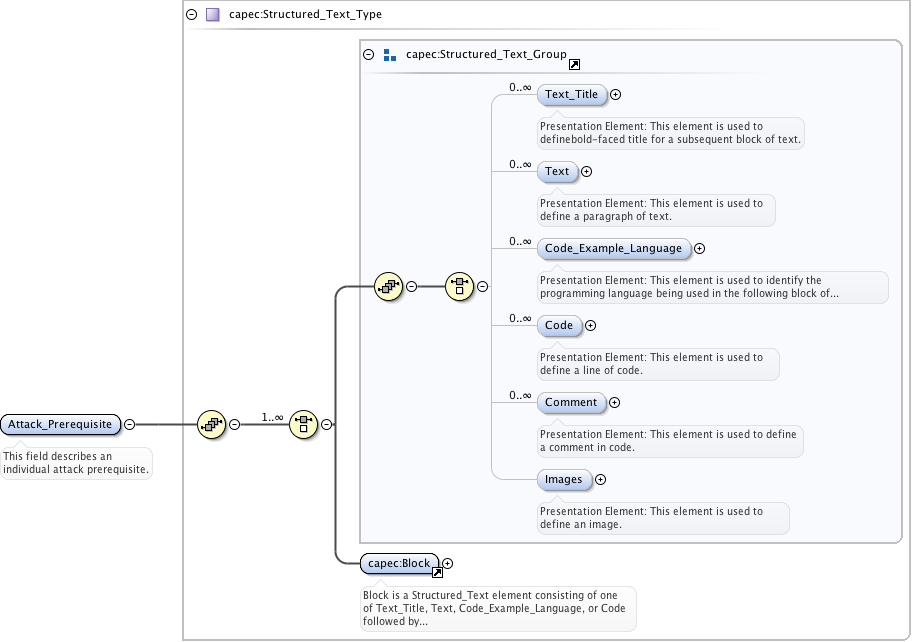
<xs:element name="Attack_Prerequisite" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>This field describes an individual attack prerequisite.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
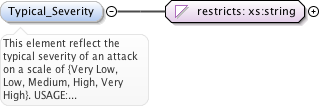
<xs:element name="Typical_Severity" minOccurs="0">
<xs:annotation>
<xs:documentation>This element reflect the typical severity of an attack on a scale of {Very Low, Low, Medium, High, Very High}. USAGE: This element is used to capture an overall typical average value for this type of attack with the understanding that it will not be completely accurate for all attacks.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Very High"/>
<xs:enumeration value="High"/>
<xs:enumeration value="Medium"/>
<xs:enumeration value="Low"/>
<xs:enumeration value="Very Low"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
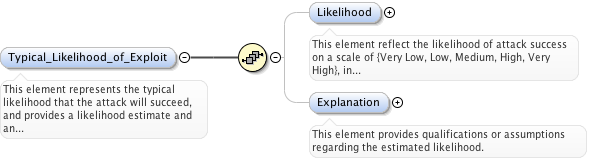
<xs:element name="Typical_Likelihood_of_Exploit" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents the typical likelihood that the attack will succeed, and provides a likelihood estimate and an explanation that qualifies the estimate. USAGE: This element is used to capture an overall typical average value for this type of attack with the understanding that it will not be completely accurate for all attacks.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
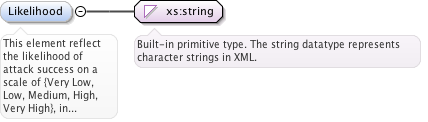
<xs:element name="Likelihood" type="xs:string" minOccurs="0">
<xs:annotation>
<xs:documentation>This element reflect the likelihood of attack success on a scale of {Very Low, Low, Medium, High, Very High}, in consideration of the attack prerequisites, targeted weakness, attack surface, skills and resources required, as well as effectiveness of likely implemented blocking solutions.</xs:documentation>
</xs:annotation>
</xs:element>
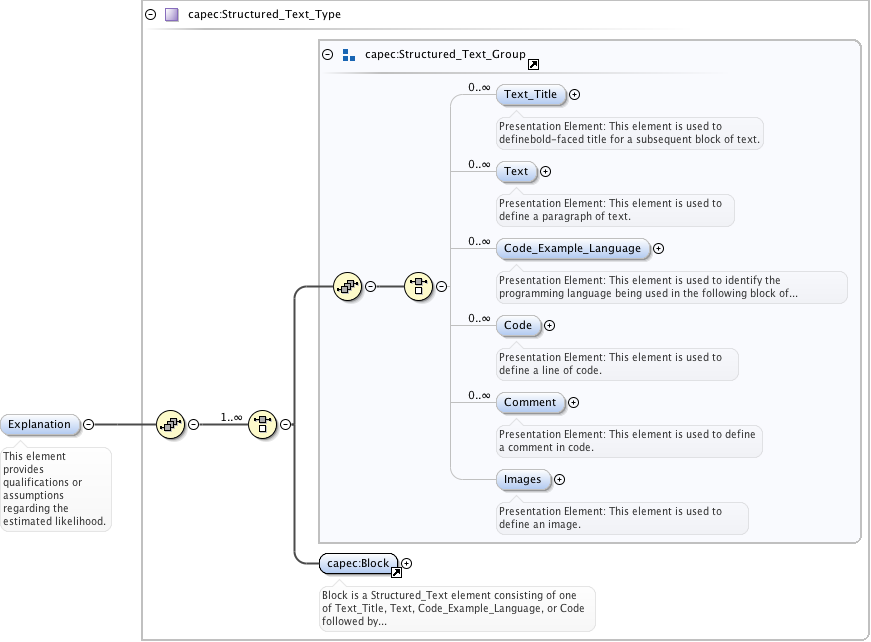
<xs:element name="Explanation" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element provides qualifications or assumptions regarding the estimated likelihood.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
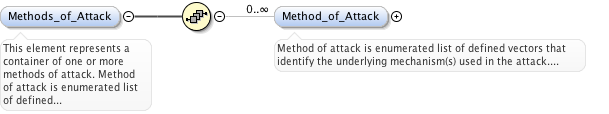
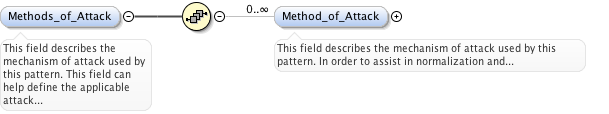
<xs:element name="Methods_of_Attack" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more methods of attack. Method of attack is enumerated list of defined vectors that identify the underlying mechanism(s) used in the attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
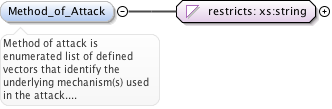
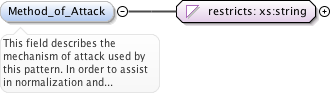
<xs:element name="Method_of_Attack" minOccurs="0" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Method of attack is enumerated list of defined vectors that identify the underlying mechanism(s) used in the attack. USAGE: This element is represented as an enumerated list to facilitate normalization and classification of attack patterns, and to help define the applicable attack surface required for this attack.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Injection"/>
<xs:enumeration value="Modification of Resources"/>
<xs:enumeration value="Protocol Manipulation"/>
<xs:enumeration value="Analysis"/>
<xs:enumeration value="API Abuse"/>
<xs:enumeration value="Brute Force"/>
<xs:enumeration value="Flooding"/>
<xs:enumeration value="Time and State"/>
<xs:enumeration value="Spoofing"/>
<xs:enumeration value="Social Engineering"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
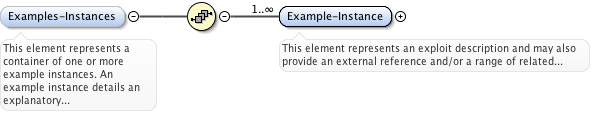
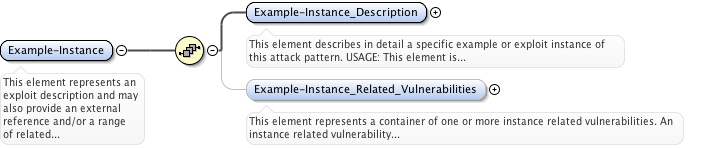
<xs:element name="Examples-Instances" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more example instances. An example instance details an explanatory example or demonstrative exploit instance of this attack, USAGE: This element is used to to help the reader understand the nature, context and variability of the attack in more practical and concrete terms.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Example-Instance" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>This element represents an exploit description and may also provide an external reference and/or a range of related vulnerabilities.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
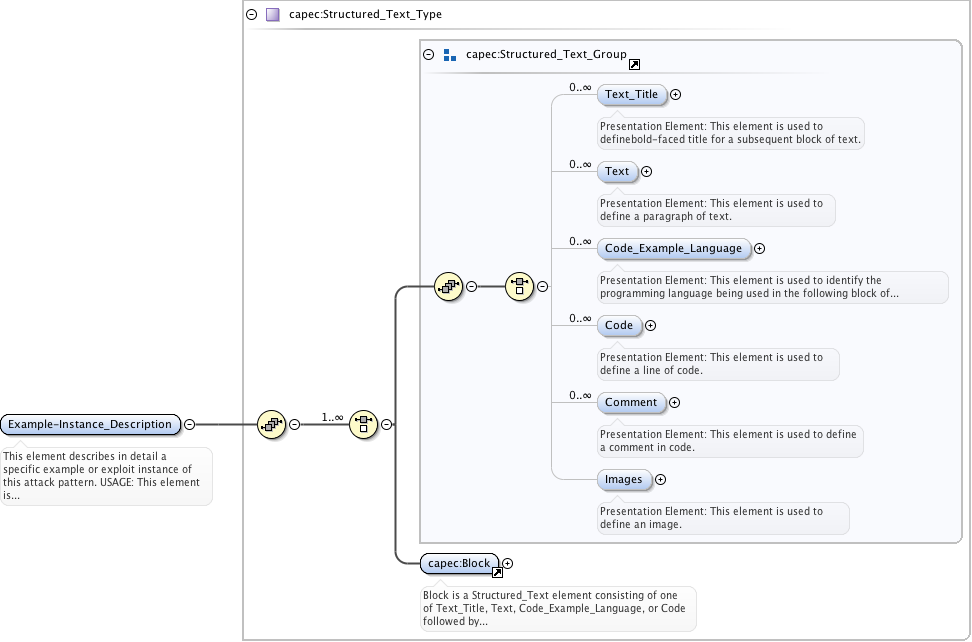
<xs:element name="Example-Instance_Description" type="capec:Structured_Text_Type">
<xs:annotation>
<xs:documentation>This element describes in detail a specific example or exploit instance of this attack pattern. USAGE: This element is used to define the context of an attack, targeted weaknesses or vulnerabilities, the sequence of attack steps, and the resulting impact of attack success or failure.</xs:documentation>
</xs:annotation>
</xs:element>
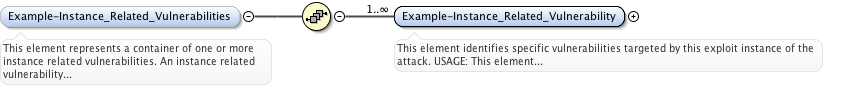
<xs:element name="Example-Instance_Related_Vulnerabilities" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more instance related vulnerabilities. An instance related vulnerability identifies vulnerabilities targeted by this exploit instance of the attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
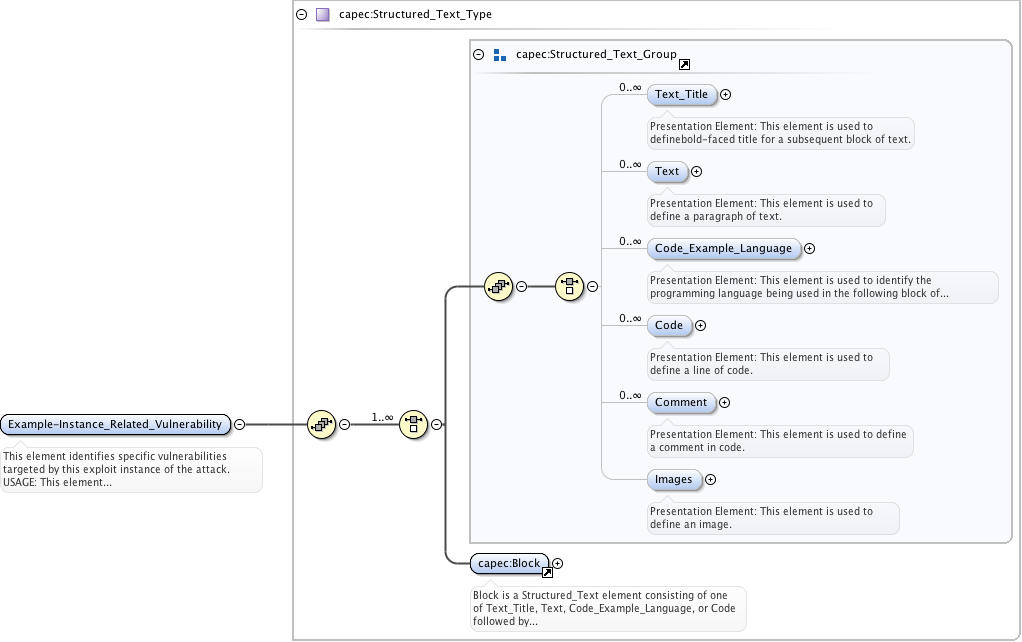
<xs:element name="Example-Instance_Related_Vulnerability" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>This element identifies specific vulnerabilities targeted by this exploit instance of the attack. USAGE: This element is used to reference industry-standard identifiers such as Common Vulnerabilities and Exposures (CVE) numbers and/or US-CERT numbers.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
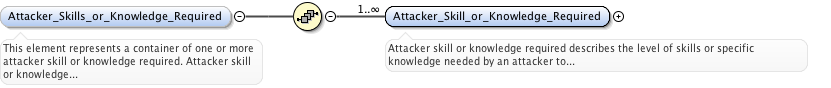
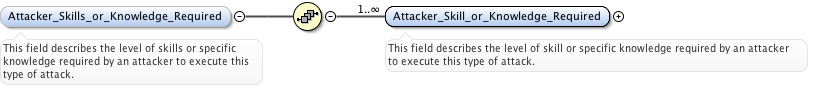
<xs:element name="Attacker_Skills_or_Knowledge_Required" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more attacker skill or knowledge required. Attacker skill or knowledge required describes the level of skills or specific knowledge needed by an attacker to execute this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
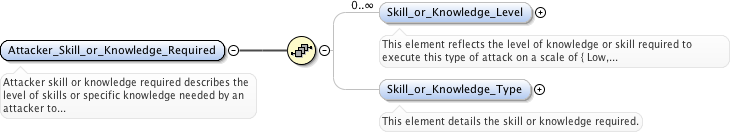
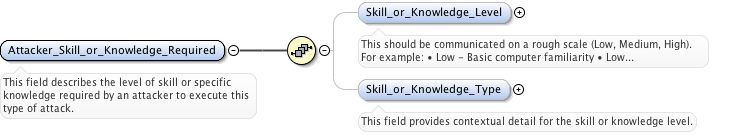
<xs:element name="Attacker_Skill_or_Knowledge_Required" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Attacker skill or knowledge required describes the level of skills or specific knowledge needed by an attacker to execute this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
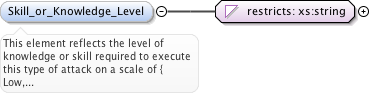
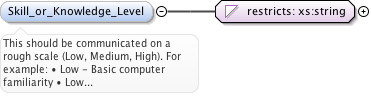
<xs:element name="Skill_or_Knowledge_Level" minOccurs="0" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>This element reflects the level of knowledge or skill required to execute this type of attack on a scale of { Low, Medium, High }. USAGE: This element is used to represent the level with respect to a specified type of skill or knowledge, e.g., low - basic SQL knowledge, high - expert knowledge of LINUX kernel, etc.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Low"/>
<xs:enumeration value="Medium"/>
<xs:enumeration value="High"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
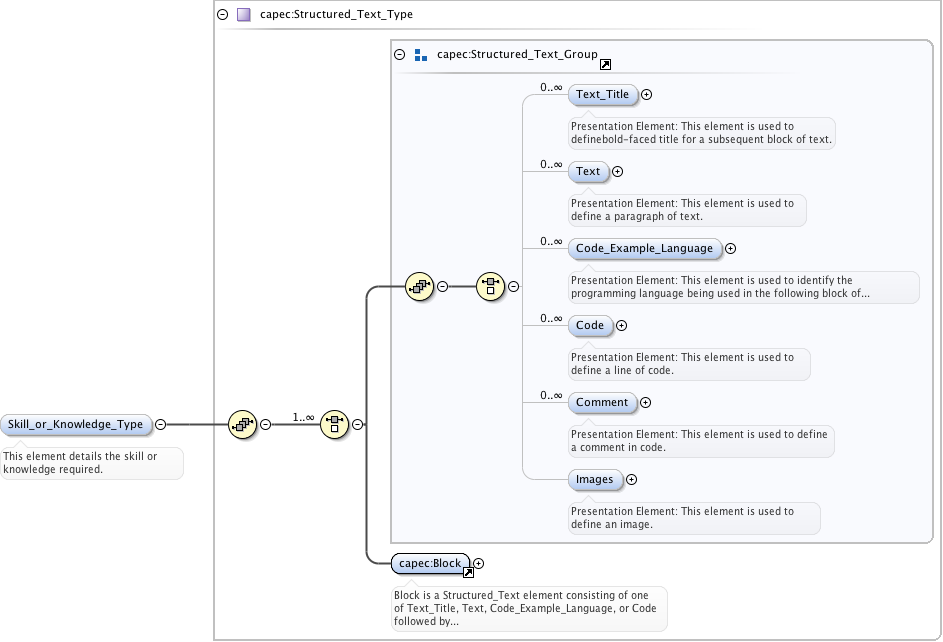
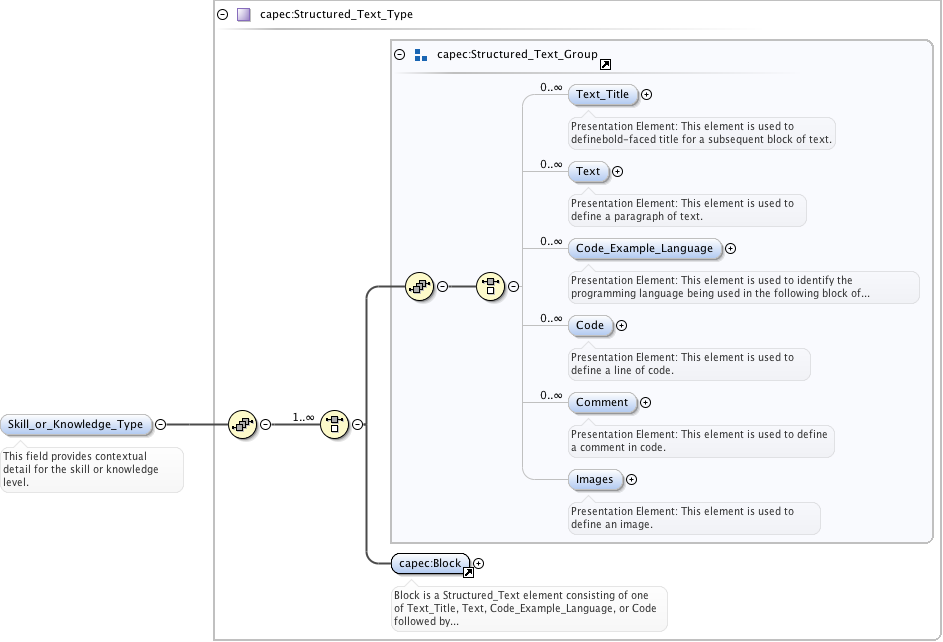
<xs:element name="Skill_or_Knowledge_Type" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element details the skill or knowledge required.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
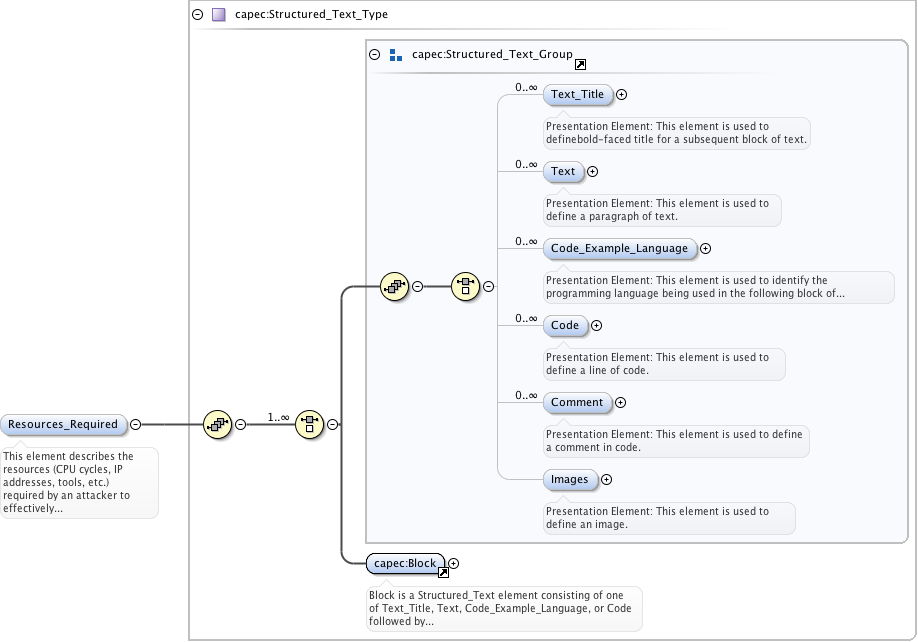
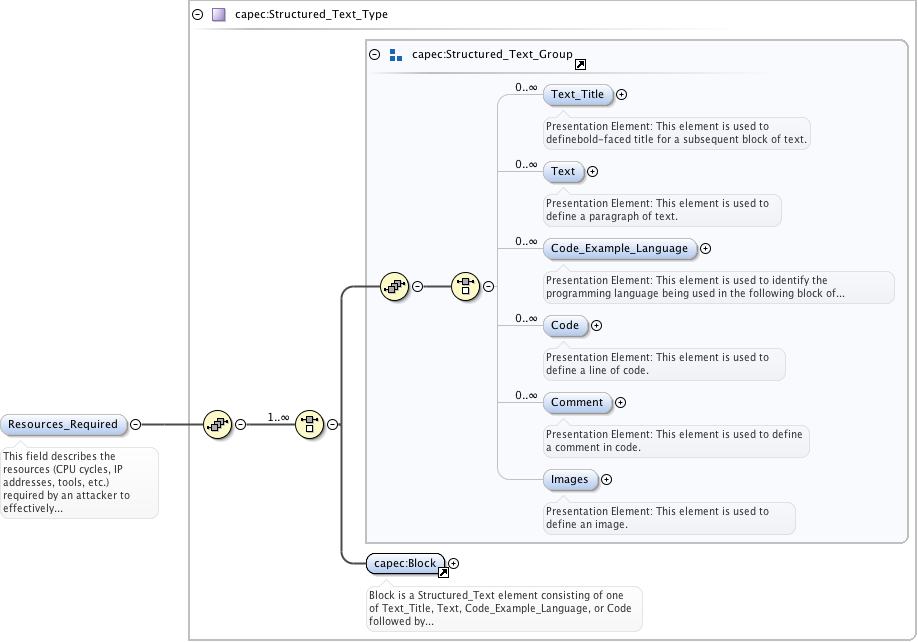
<xs:element name="Resources_Required" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the resources (CPU cycles, IP addresses, tools, etc.) required by an attacker to effectively execute this type of attack.</xs:documentation>
</xs:annotation>
</xs:element>
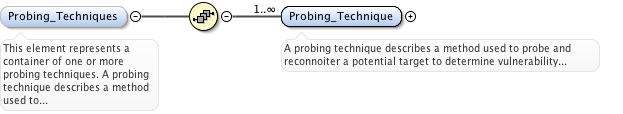
<xs:element name="Probing_Techniques" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more probing techniques. A probing technique describes a method used to probe and reconnoiter a potential target to determine vulnerability and/or to prepare for this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Probing_Technique" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A probing technique describes a method used to probe and reconnoiter a potential target to determine vulnerability and/or to prepare for this type of attack.</xs:documentation>
</xs:annotation>
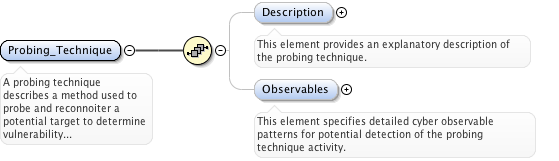
<xs:complexType>
<xs:sequence>
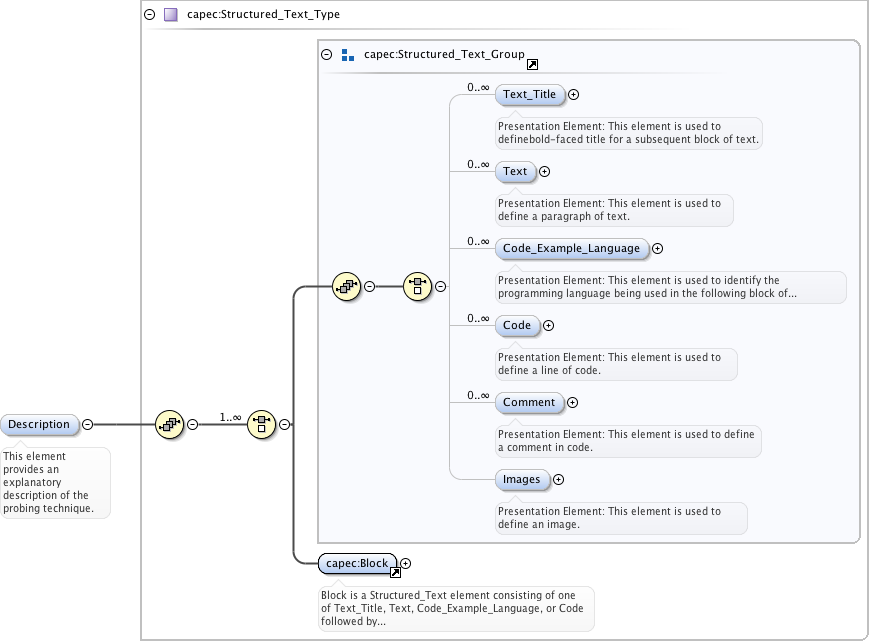
<xs:element name="Description" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element provides an explanatory description of the probing technique.</xs:documentation>
</xs:annotation>
</xs:element>
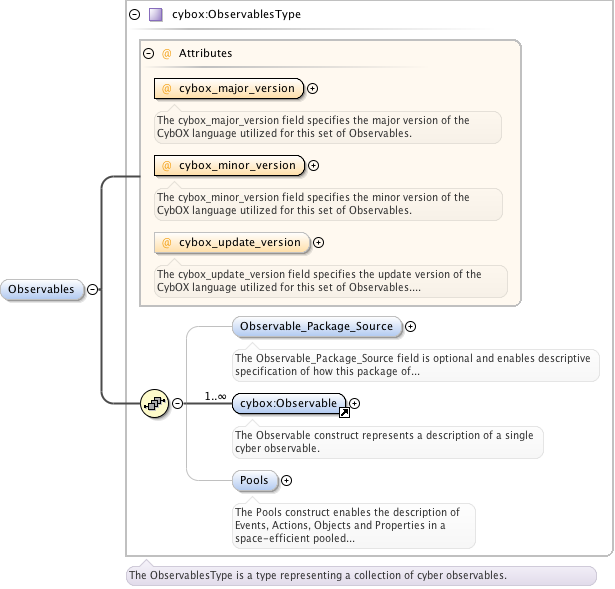
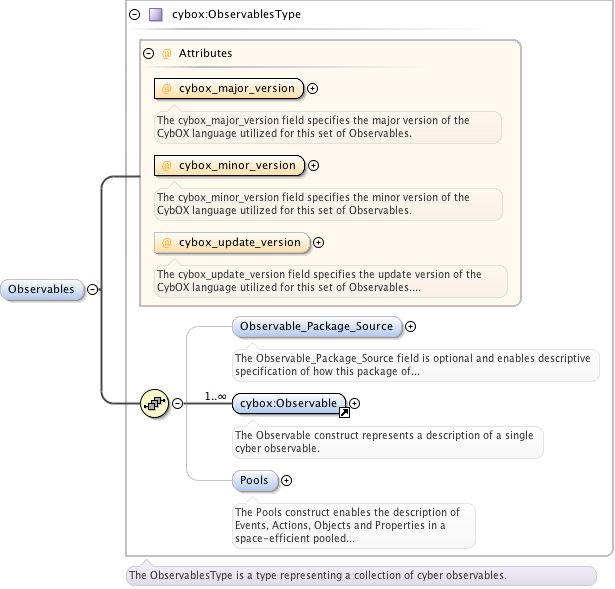
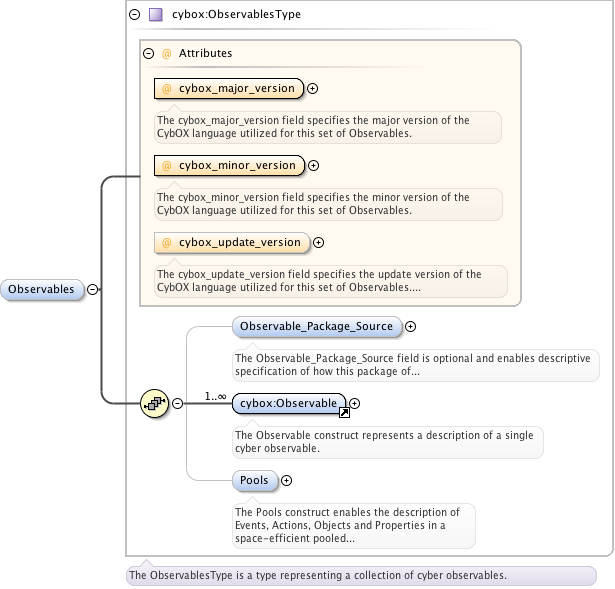
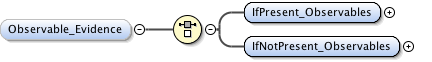
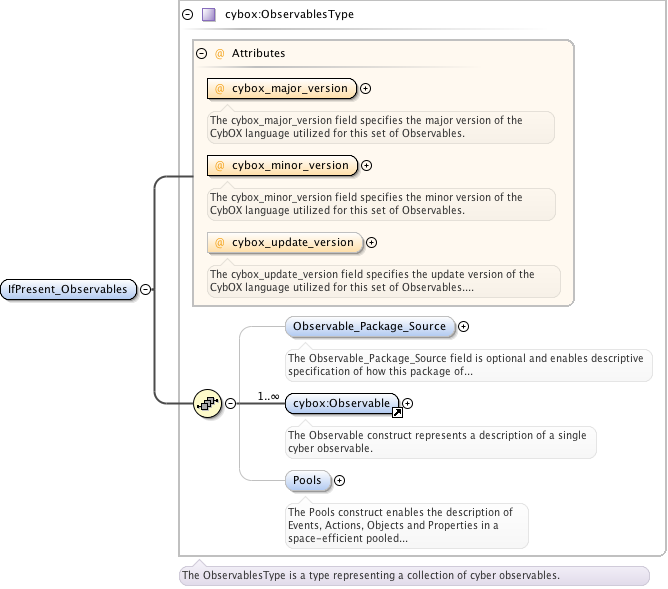
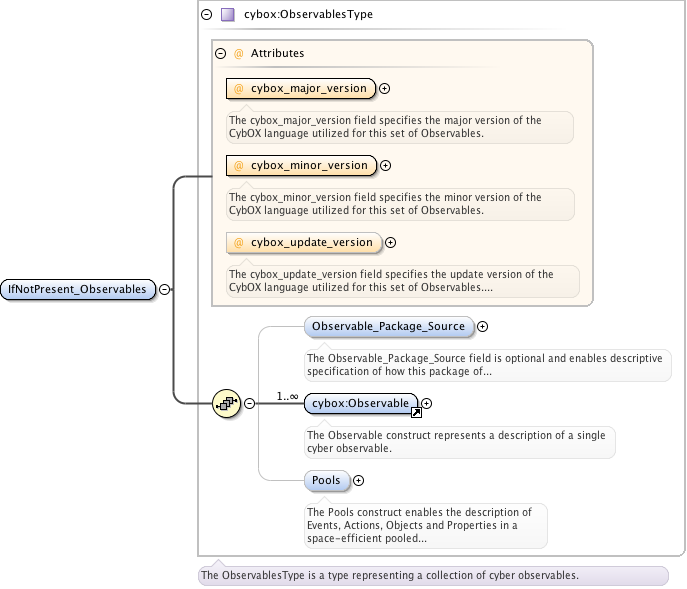
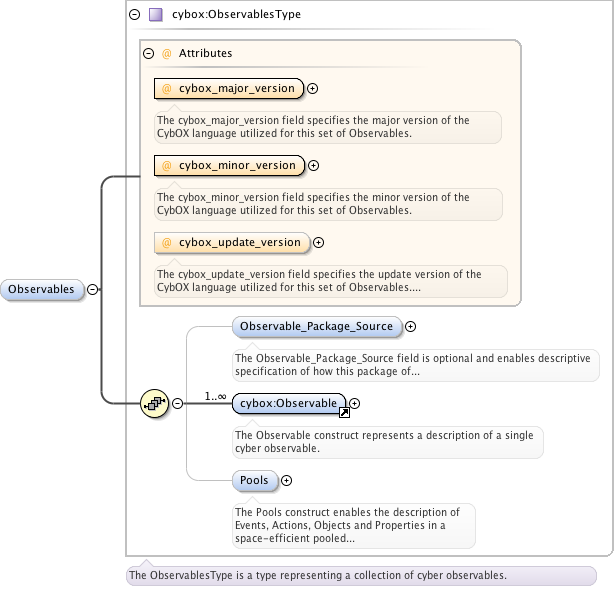
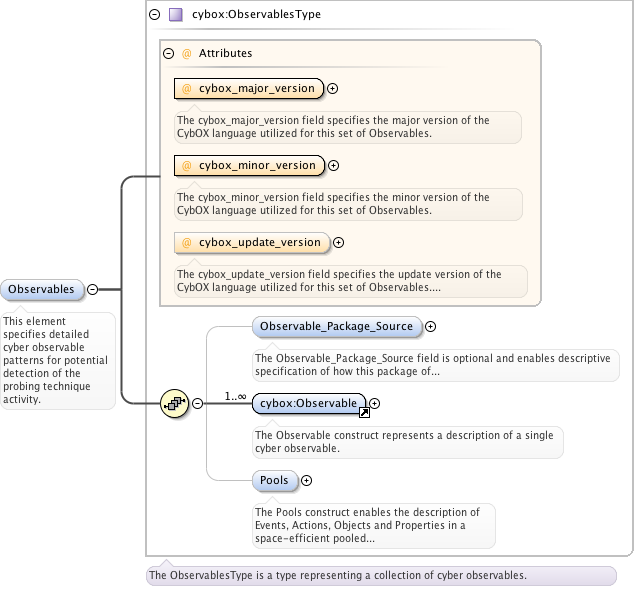
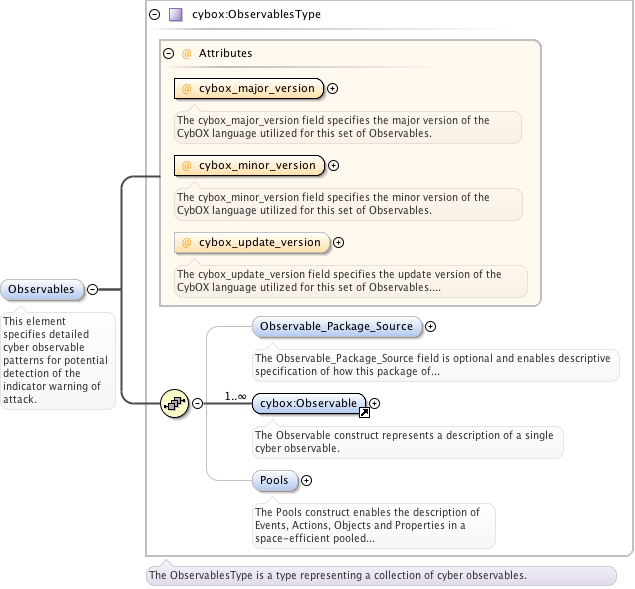
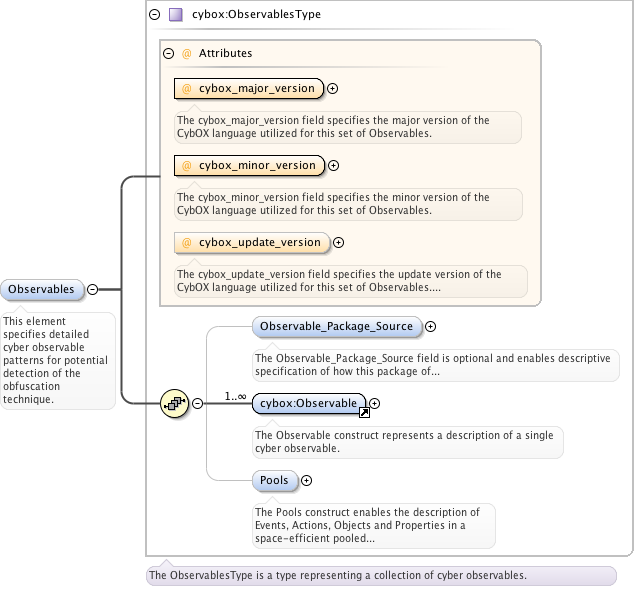
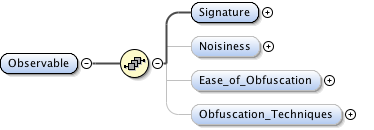
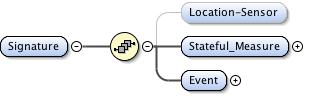
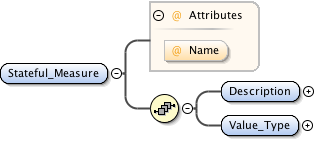
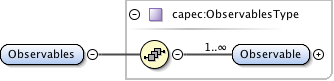
<xs:element name="Observables" type="cybox:ObservablesType" minOccurs="0">
<xs:annotation>
<xs:documentation>This element specifies detailed cyber observable patterns for potential detection of the probing technique activity.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
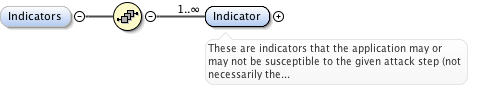
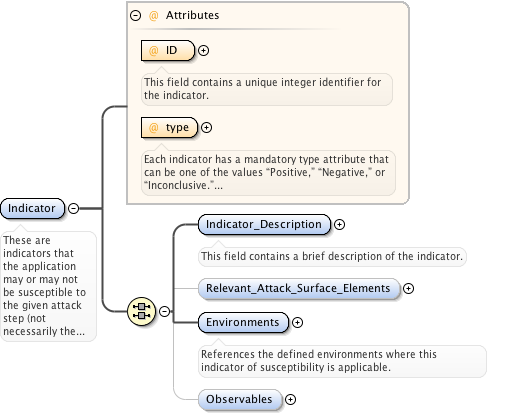
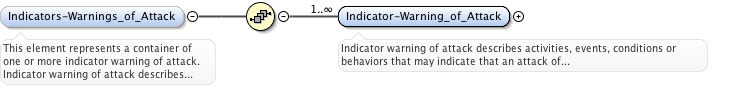
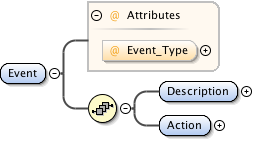
<xs:element name="Indicators-Warnings_of_Attack" minOccurs="0">
<xs:annotation>
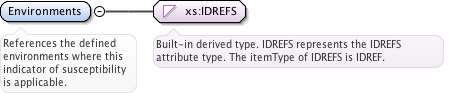
<xs:documentation>This element represents a container of one or more indicator warning of attack. Indicator warning of attack describes activities, events, conditions or behaviors that may indicate that an attack of this type is imminent, in progress or has occurred.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Indicator-Warning_of_Attack" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Indicator warning of attack describes activities, events, conditions or behaviors that may indicate that an attack of this type is imminent, in progress or has occurred.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
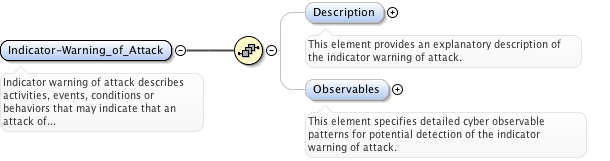
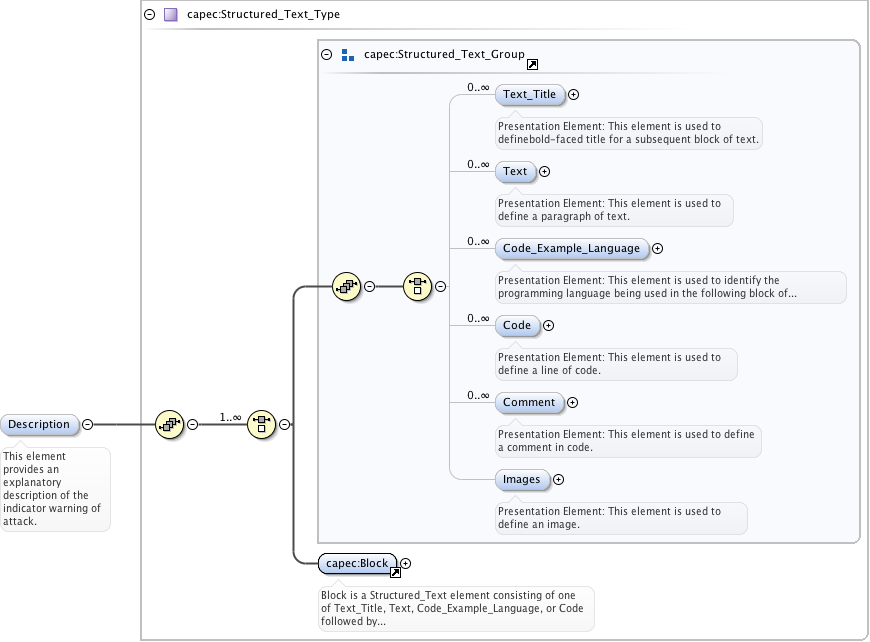
<xs:element name="Description" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element provides an explanatory description of the indicator warning of attack.</xs:documentation>
</xs:annotation>
</xs:element>
<xs:element name="Observables" type="cybox:ObservablesType" minOccurs="0">
<xs:annotation>
<xs:documentation>This element specifies detailed cyber observable patterns for potential detection of the indicator warning of attack.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
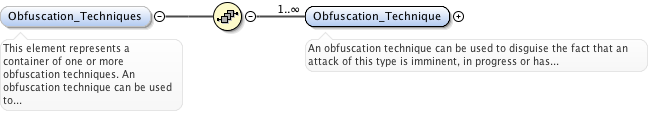
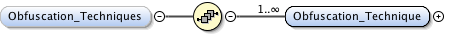
<xs:element name="Obfuscation_Techniques" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more obfuscation techniques. An obfuscation technique can be used to disguise the fact that an attack of this type is imminent, in progress or has occurred.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
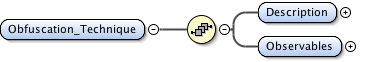
<xs:element name="Obfuscation_Technique" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>An obfuscation technique can be used to disguise the fact that an attack of this type is imminent, in progress or has occurred.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
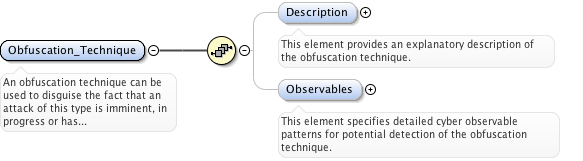
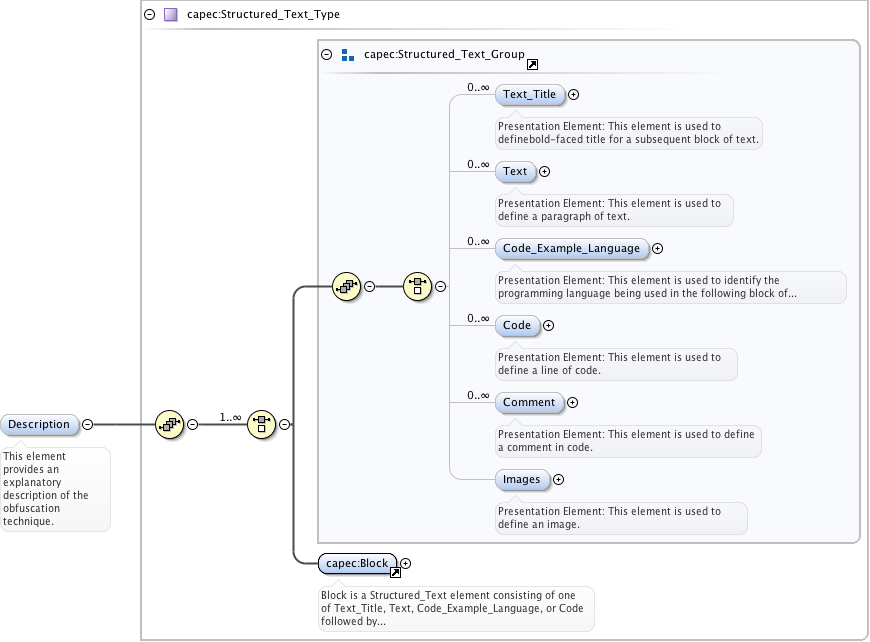
<xs:element name="Description" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element provides an explanatory description of the obfuscation technique.</xs:documentation>
</xs:annotation>
</xs:element>
<xs:element name="Observables" type="cybox:ObservablesType" minOccurs="0">
<xs:annotation>
<xs:documentation>This element specifies detailed cyber observable patterns for potential detection of the obfuscation technique.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
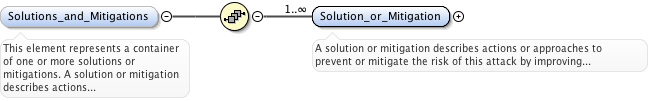
<xs:element name="Solutions_and_Mitigations" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more solutions or mitigations. A solution or mitigation describes actions or approaches to prevent or mitigate the risk of this attack by improving the resilience of the target system, reduce its attack surface or to reduce the impact of the attack if it is successful.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Solution_or_Mitigation" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A solution or mitigation describes actions or approaches to prevent or mitigate the risk of this attack by improving the resilience of the target system, reduce its attack surface or to reduce the impact of the attack if it is successful.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
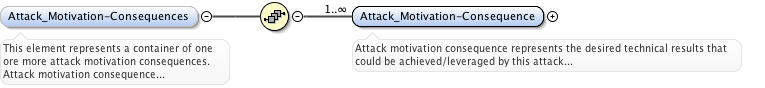
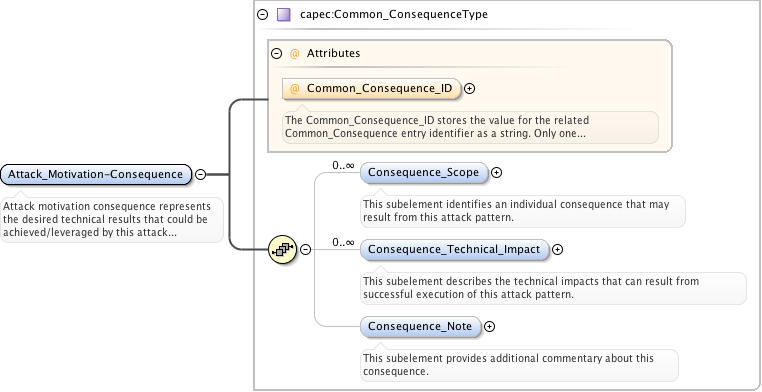
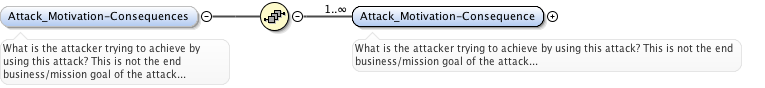
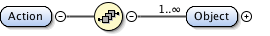
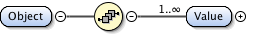
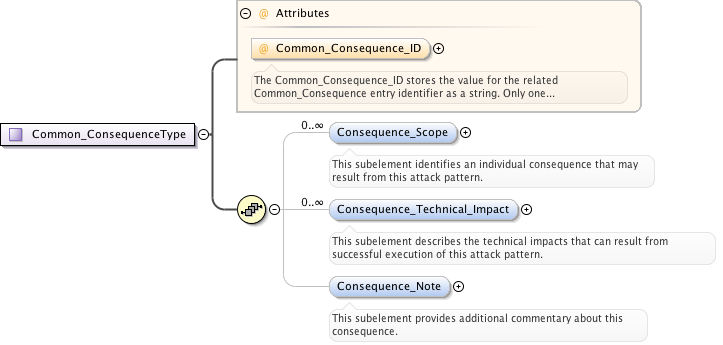
<xs:element name="Attack_Motivation-Consequences" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one ore more attack motivation consequences. Attack motivation consequence represents the desired technical results that could be achieved/leveraged by this attack pattern, represented as an enumerated list of defined adversary motivations/consequences. USAGE: This element is used to identify specific technical results that could be leveraged to achieve the adversary's business or mission objective. This information is useful for aligning attack patterns to threat models and for determining which attack patterns are relevant for a given context.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
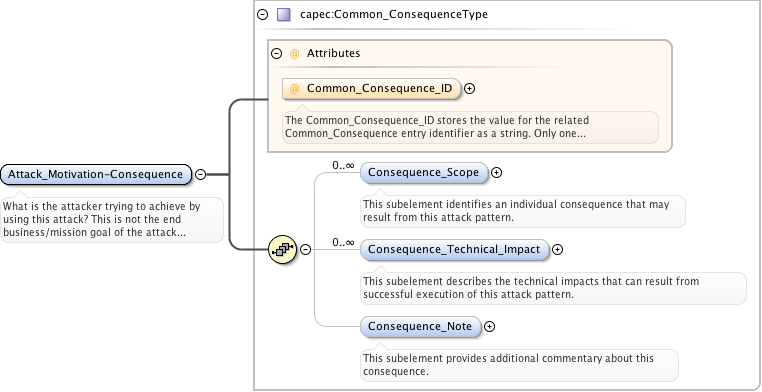
<xs:element name="Attack_Motivation-Consequence" type="capec:Common_ConsequenceType" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Attack motivation consequence represents the desired technical results that could be achieved/leveraged by this attack pattern, represented as an enumerated list of defined adversary motivations/consequences.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
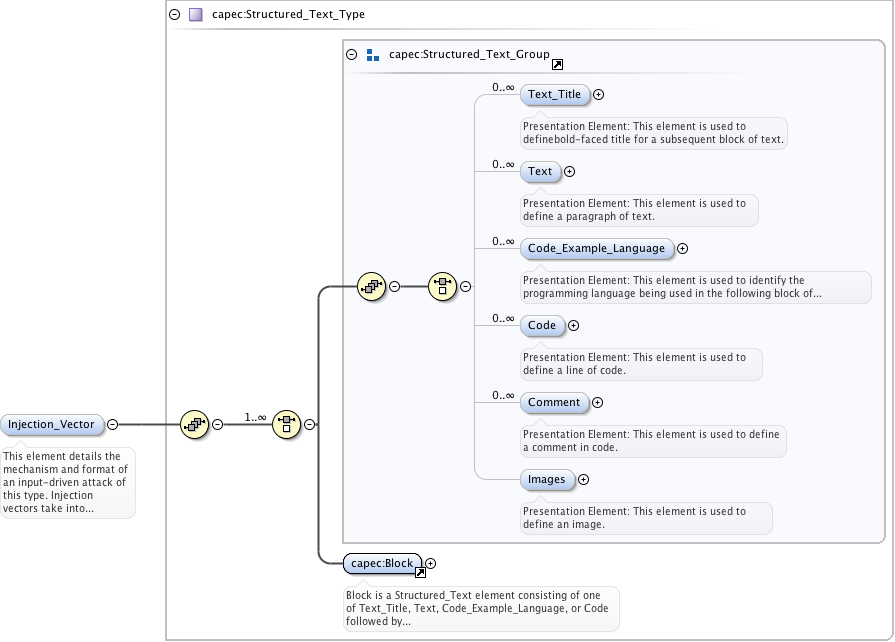
<xs:element name="Injection_Vector" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element details the mechanism and format of an input-driven attack of this type. Injection vectors take into account the grammar of an attack, the syntax accepted by the system, the position of various fields, and the ranges of data that are acceptable.</xs:documentation>
</xs:annotation>
</xs:element>
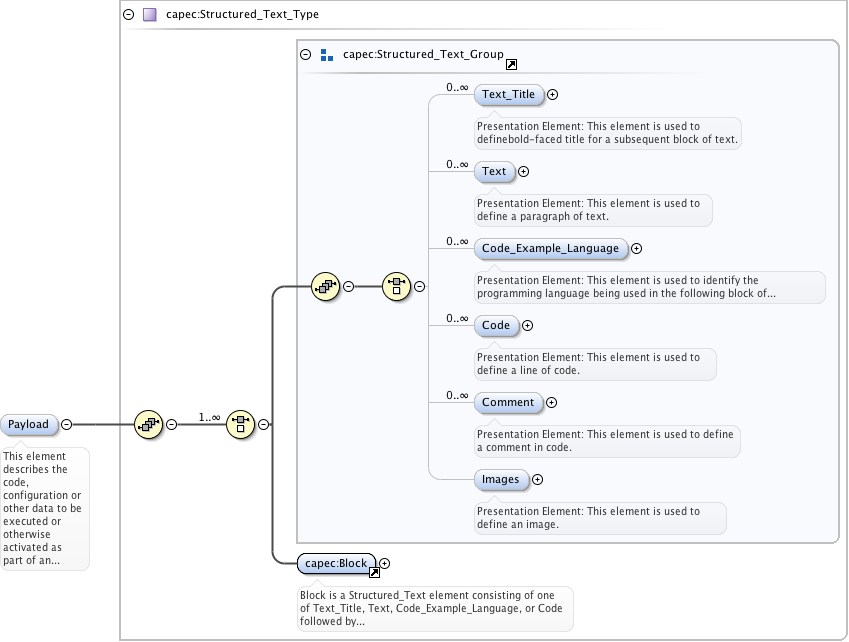
<xs:element name="Payload" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the code, configuration or other data to be executed or otherwise activated as part of an injection-based attack of this type.</xs:documentation>
</xs:annotation>
</xs:element>
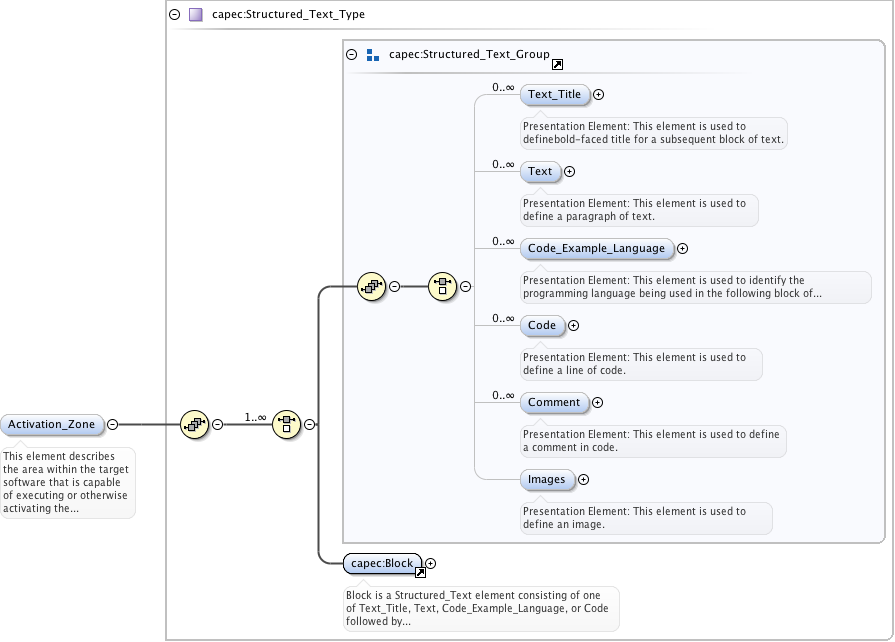
<xs:element name="Activation_Zone" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the area within the target software that is capable of executing or otherwise activating the payload of an injection-based attack of this type. The activation zone is where the intent of the attacker is put into action. The activation zone may be a command interpreter, some active machine code in a buffer, a client browser, a system API call, etc.</xs:documentation>
</xs:annotation>
</xs:element>
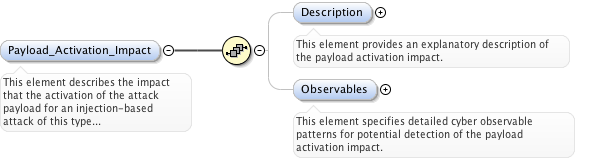
<xs:element name="Payload_Activation_Impact" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the impact that the activation of the attack payload for an injection-based attack of this type would typically have on the confidentiality, integrity or availability of the target software.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
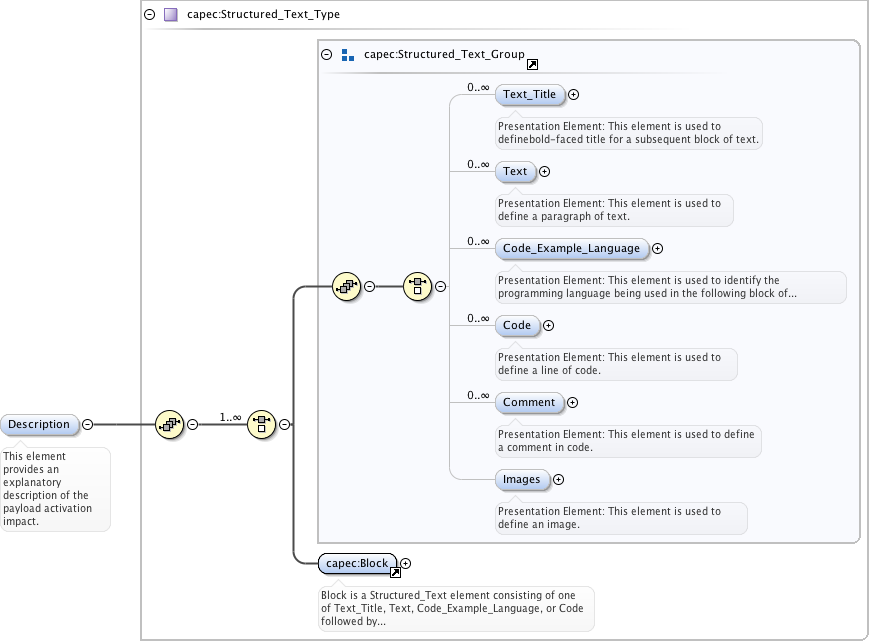
<xs:element name="Description" type="capec:Structured_Text_Type" minOccurs="0">
<xs:annotation>
<xs:documentation>This element provides an explanatory description of the payload activation impact.</xs:documentation>
</xs:annotation>
</xs:element>
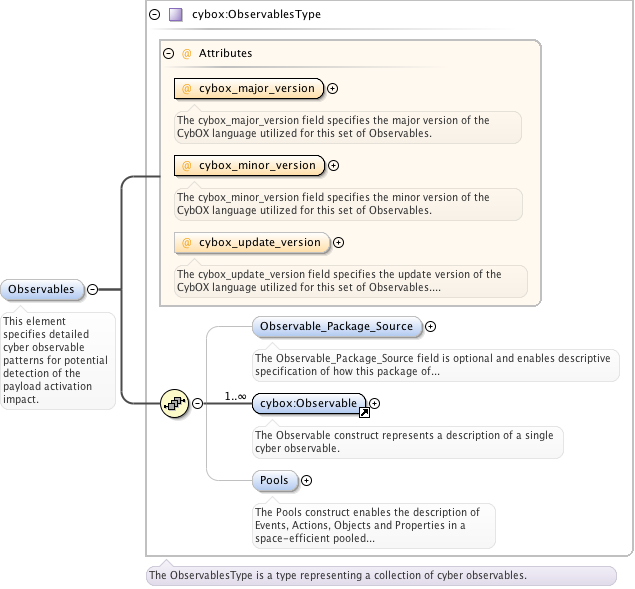
<xs:element name="Observables" type="cybox:ObservablesType" minOccurs="0">
<xs:annotation>
<xs:documentation>This element specifies detailed cyber observable patterns for potential detection of the payload activation impact.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
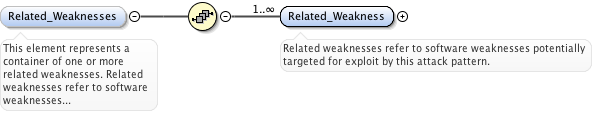
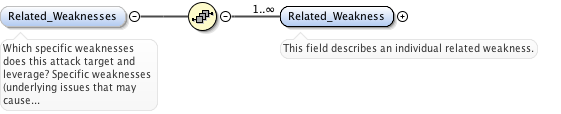
<xs:element name="Related_Weaknesses" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more related weaknesses. Related weaknesses refer to software weaknesses potentially targeted for exploit by this attack pattern. USAGE: This element is used to reference industry standard Common Weakness Enumeration (CWE) data, including weaknesses that are exploited by the attack as well as weaknesses whose presence increases the likelihood or impact of the attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
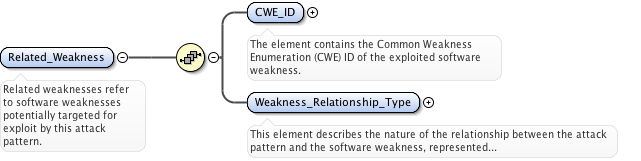
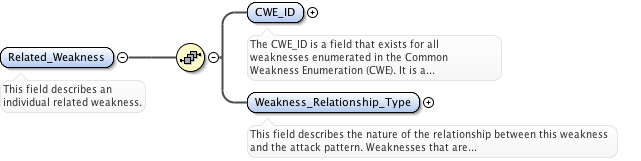
<xs:element name="Related_Weakness" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Related weaknesses refer to software weaknesses potentially targeted for exploit by this attack pattern.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
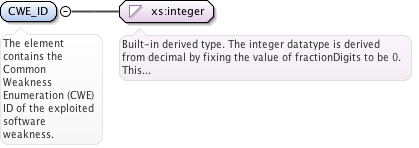
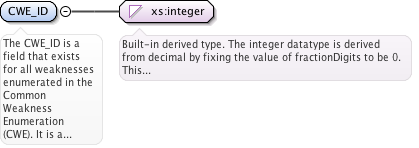
<xs:element name="CWE_ID" type="xs:integer">
<xs:annotation>
<xs:documentation>The element contains the Common Weakness Enumeration (CWE) ID of the exploited software weakness.</xs:documentation>
</xs:annotation>
</xs:element>
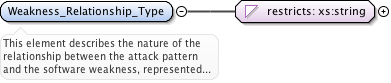
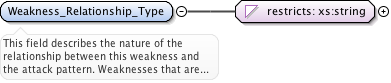
<xs:element name="Weakness_Relationship_Type">
<xs:annotation>
<xs:documentation>This element describes the nature of the relationship between the attack pattern and the software weakness, represented as the enumerated list {Targeted, Secondary}. USAGE: This element is used to indicate whether the weakness is targeted or secondary. If the attack is designed to exploit the weakness, then that weakness is Targeted. A weaknesses whose presence may increase the likelihood of the attack succeeding or the impact of the attack if it does succeed is Secondary.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Targeted"/>
<xs:enumeration value="Secondary"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
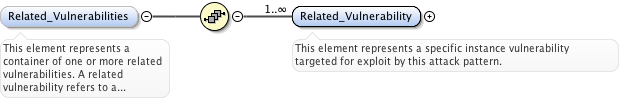
<xs:element name="Related_Vulnerabilities" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more related vulnerabilities. A related vulnerability refers to a specific instance vulnerability targeted for exploit by this attack pattern. USAGE: This element is used to identify specific vulnerabilities by their industry-standard Common Vulnerabilities and Exposures (CVE) numbers and/or US-CERT numbers. As vulnerabilities are much more specific and localized than weaknesses, it is uncommon that an attack pattern would target a specific vulnerability. This would most likely occur if the attack pattern were targeting vulnerabilities in the underlying platform, framework, or software library.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
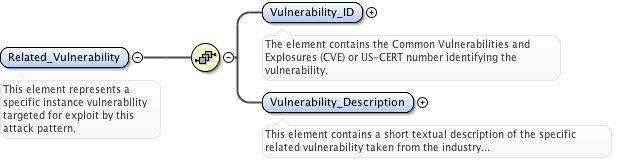
<xs:element name="Related_Vulnerability" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>This element represents a specific instance vulnerability targeted for exploit by this attack pattern.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
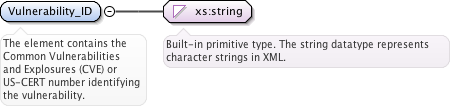
<xs:element name="Vulnerability_ID" type="xs:string">
<xs:annotation>
<xs:documentation>The element contains the Common Vulnerabilities and Explosures (CVE) or US-CERT number identifying the vulnerability.</xs:documentation>
</xs:annotation>
</xs:element>
<xs:element name="Vulnerability_Description" type="capec:Structured_Text_Type">
<xs:annotation>
<xs:documentation>This element contains a short textual description of the specific related vulnerability taken from the industry standard vulnerability listing.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
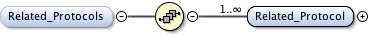
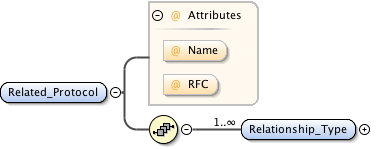
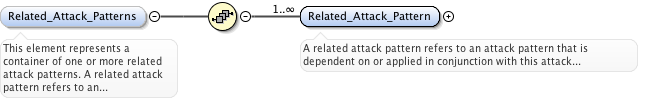
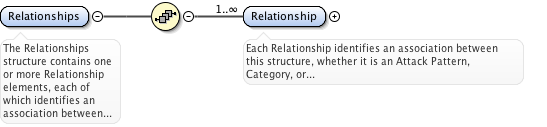
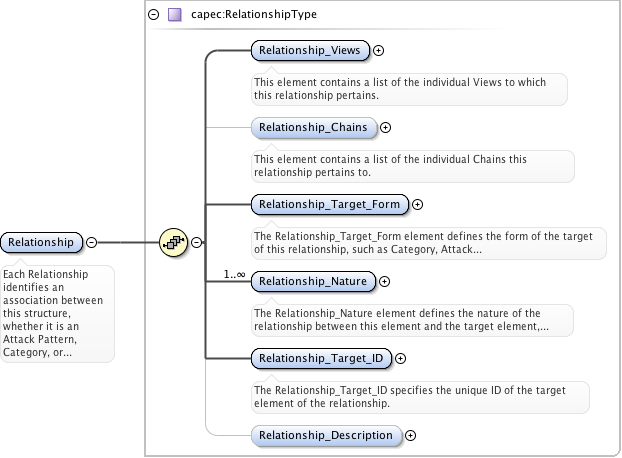
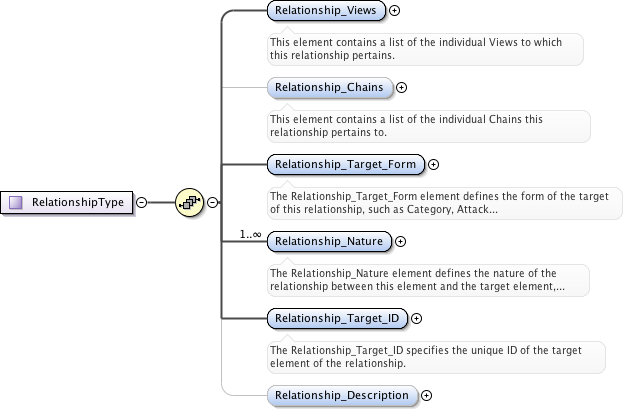
<xs:element name="Related_Attack_Patterns" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more related attack patterns. A related attack pattern refers to an attack pattern that is dependent on or applied in conjunction with this attack pattern.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
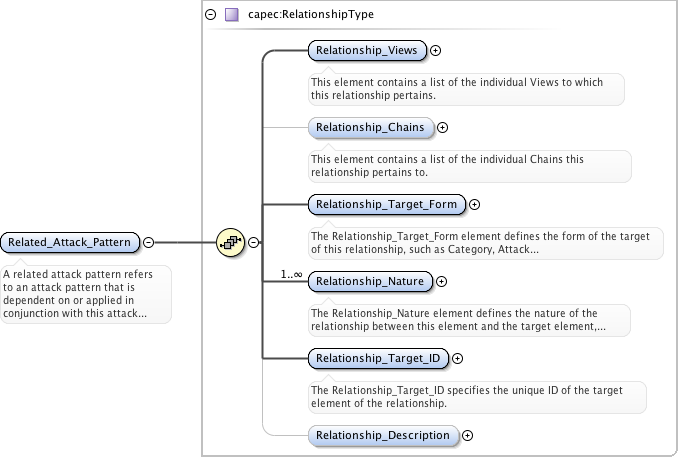
<xs:element name="Related_Attack_Pattern" type="capec:RelationshipType" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A related attack pattern refers to an attack pattern that is dependent on or applied in conjunction with this attack pattern.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
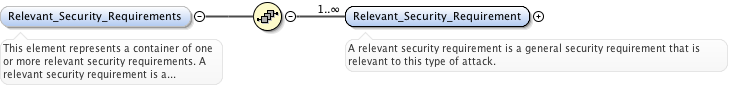
<xs:element name="Relevant_Security_Requirements" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more relevant security requirements. A relevant security requirement is a general security requirement that is relevant to this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Relevant_Security_Requirement" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A relevant security requirement is a general security requirement that is relevant to this type of attack.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
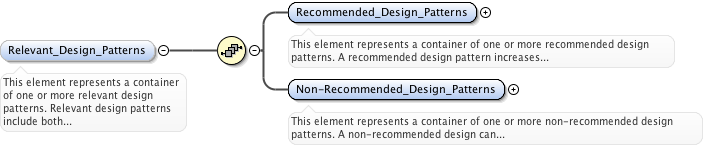
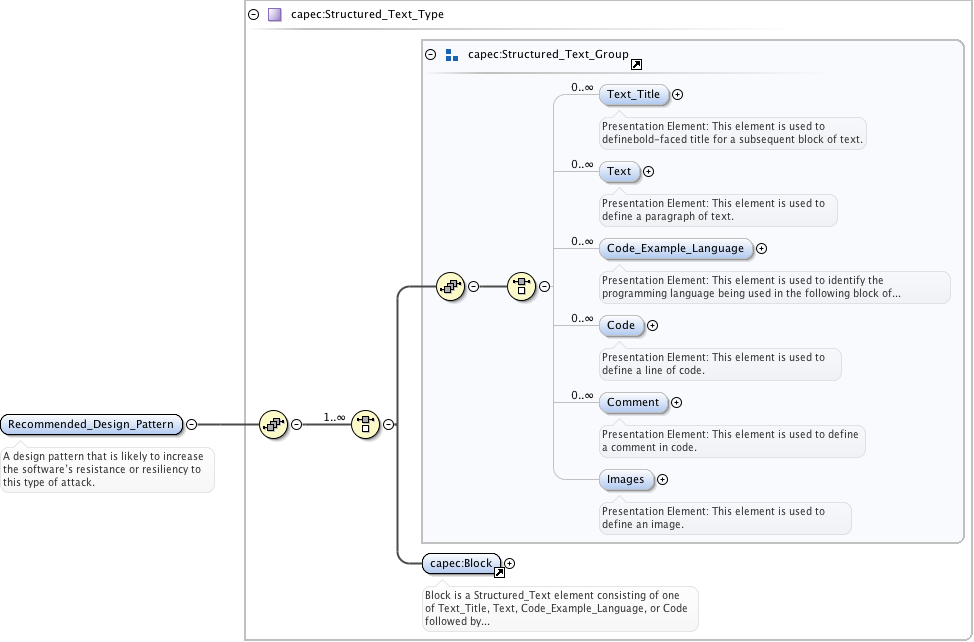
<xs:element name="Relevant_Design_Patterns" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more relevant design patterns. Relevant design patterns include both recommended design patterns, which increase the software's resistance or resilience to this type of attack, and non-recommended design patterns, which could leave the system especially susceptible to this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
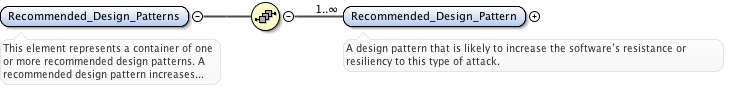
<xs:element name="Recommended_Design_Patterns">
<xs:annotation>
<xs:documentation>This element represents a container of one or more recommended design patterns. A recommended design pattern increases the software's resistance or resilience to this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Recommended_Design_Pattern" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A design pattern that is likely to increase the software’s resistance or resiliency to this type of attack.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
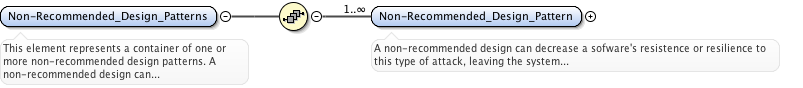
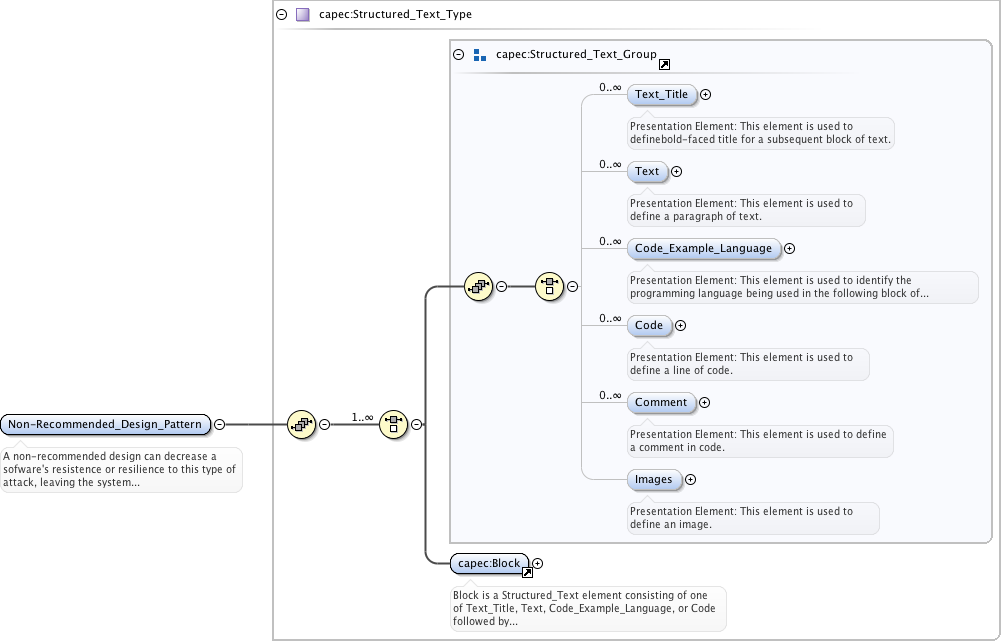
<xs:element name="Non-Recommended_Design_Patterns">
<xs:annotation>
<xs:documentation>This element represents a container of one or more non-recommended design patterns. A non-recommended design can decrease a sofware's resistence or resilience to this type of attack, leaving the system more susceptible.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Non-Recommended_Design_Pattern" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A non-recommended design can decrease a sofware's resistence or resilience to this type of attack, leaving the system more susceptible.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
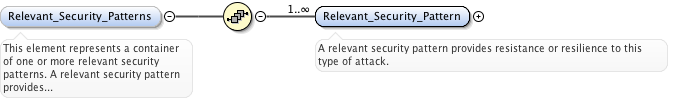
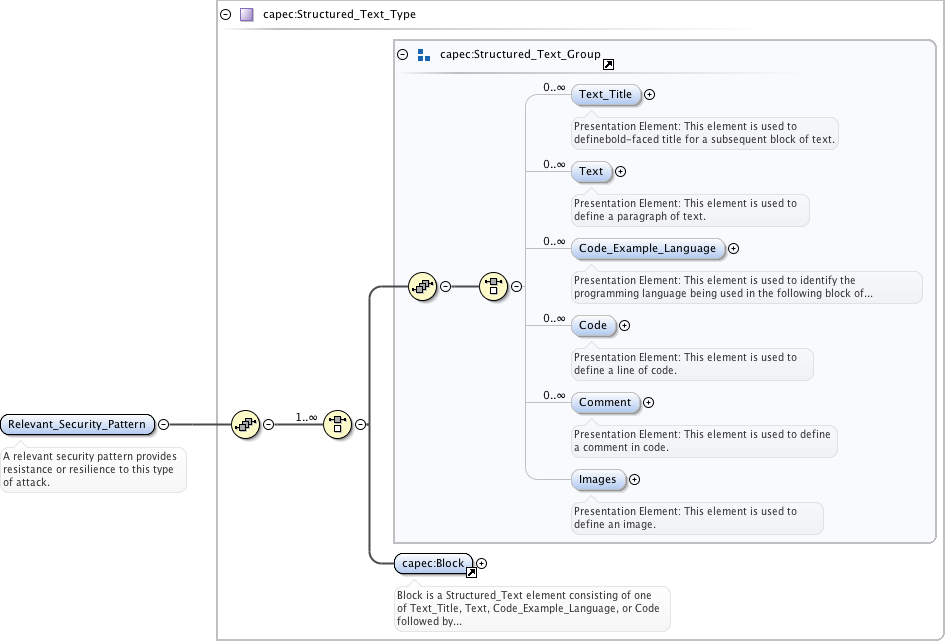
<xs:element name="Relevant_Security_Patterns" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more relevant security patterns. A relevant security pattern provides resistance or resilience to this type of attack.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Relevant_Security_Pattern" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A relevant security pattern provides resistance or resilience to this type of attack.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
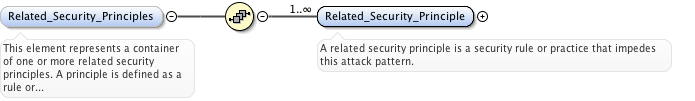
<xs:element name="Related_Security_Principles" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more related security principles. A principle is defined as a rule or standard for good behavior. A related security principle is a security rule or practice that impedes this attack pattern. USAGE: Usage defined in NIST SP 800-27A, "Engineering Principles for Information Technology Security", Revision A.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
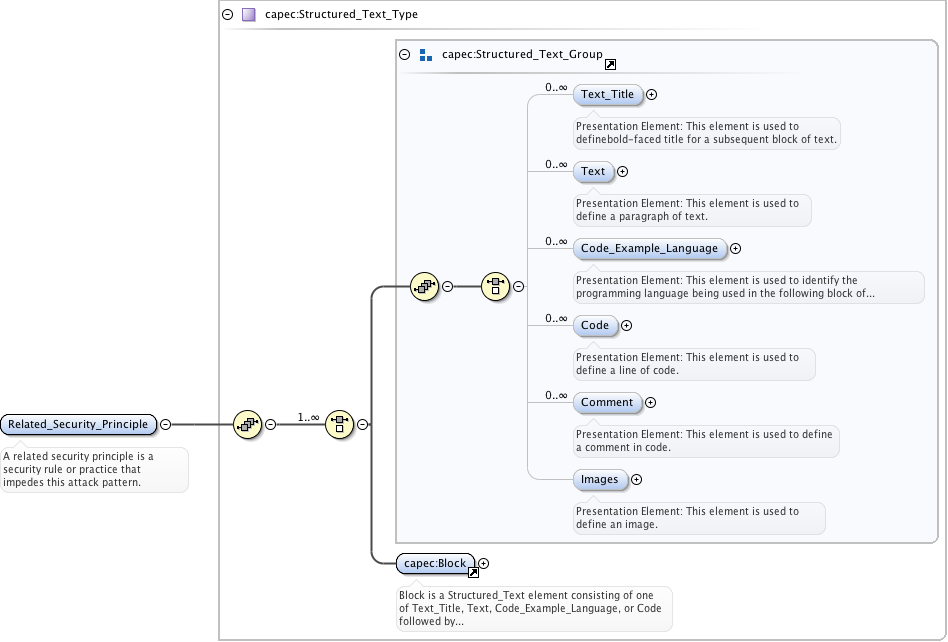
<xs:element name="Related_Security_Principle" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A related security principle is a security rule or practice that impedes this attack pattern.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
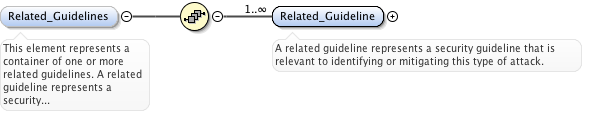
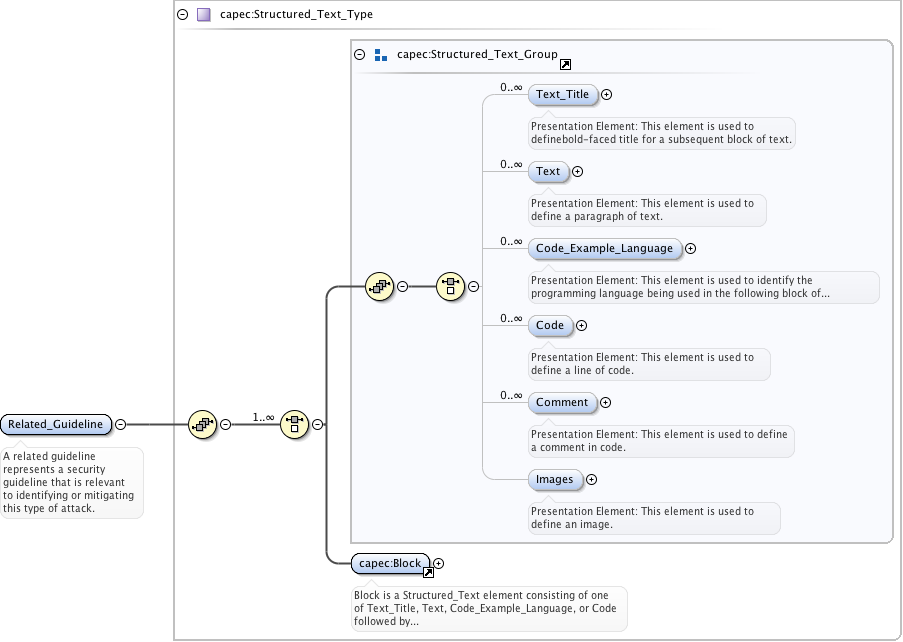
<xs:element name="Related_Guidelines" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more related guidelines. A related guideline represents a security guideline that is relevant to identifying or mitigating this type of attack. USAGE: It would be helpful to provide a usage reference. However links to security principle and guideline documentation on the BSI site appear to be broken. NIST SP 800-27 uses the terms principle and guideline interchangeably.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Related_Guideline" type="capec:Structured_Text_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>A related guideline represents a security guideline that is relevant to identifying or mitigating this type of attack.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
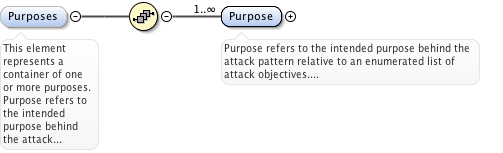
<xs:element name="Purposes" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more purposes. Purpose refers to the intended purpose behind the attack pattern relative to an enumerated list of attack objectives. USAGE: This element is used to capture pattern composibility and assist with normalization and classification of attack patterns within the CAPEC catalog.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
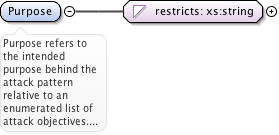
<xs:element name="Purpose" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Purpose refers to the intended purpose behind the attack pattern relative to an enumerated list of attack objectives. USAGE: This element is represented as an enumerated list to facilitate normalization and classification of attack patterns</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Reconnaissance"/>
<xs:enumeration value="Penetration"/>
<xs:enumeration value="Exploitation"/>
<xs:enumeration value="Obfuscation"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
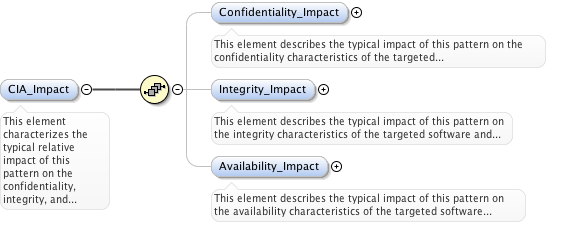
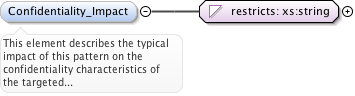
<xs:element name="CIA_Impact" minOccurs="0">
<xs:annotation>
<xs:documentation>This element characterizes the typical relative impact of this pattern on the confidentiality, integrity, and availability of the targeted software.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Confidentiality_Impact" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the typical impact of this pattern on the confidentiality characteristics of the targeted software and related data.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Low"/>
<xs:enumeration value="Medium"/>
<xs:enumeration value="High"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
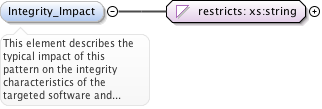
<xs:element name="Integrity_Impact" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the typical impact of this pattern on the integrity characteristics of the targeted software and related data.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Low"/>
<xs:enumeration value="Medium"/>
<xs:enumeration value="High"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
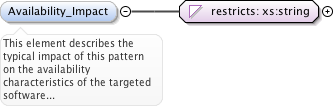
<xs:element name="Availability_Impact" minOccurs="0">
<xs:annotation>
<xs:documentation>This element describes the typical impact of this pattern on the availability characteristics of the targeted software and related data.</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Low"/>
<xs:enumeration value="Medium"/>
<xs:enumeration value="High"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
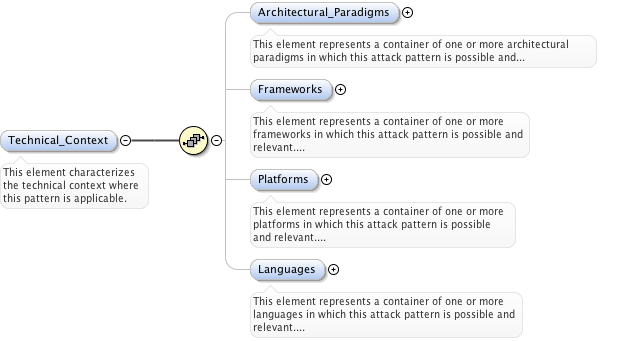
<xs:element name="Technical_Context" minOccurs="0">
<xs:annotation>
<xs:documentation>This element characterizes the technical context where this pattern is applicable.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
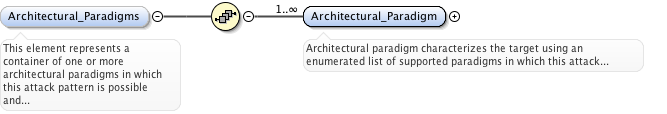
<xs:element name="Architectural_Paradigms" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more architectural paradigms in which this attack pattern is possible and relevant. Architectural paradigm characterizes the target using an enumerated list of paradigms utilized by the target.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
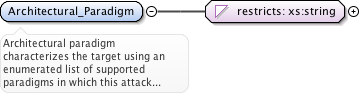
<xs:element name="Architectural_Paradigm" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Architectural paradigm characterizes the target using an enumerated list of supported paradigms in which this attack pattern is possible and relevant. USAGE: This element is represented as an enumerated list to facilitate normalization and classification of attack patterns</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Mainframe"/>
<xs:enumeration value="Client-Server"/>
<xs:enumeration value="n-Tier"/>
<xs:enumeration value="Web"/>
<xs:enumeration value="SOA"/>
<xs:enumeration value="Other"/>
<xs:enumeration value="All"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
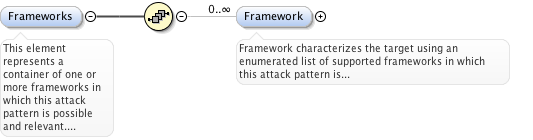
<xs:element name="Frameworks" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more frameworks in which this attack pattern is possible and relevant. Frameworks characterizes the target using an enumerated list of frameworks utilized by the target.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
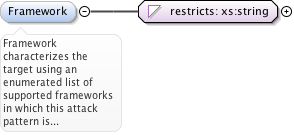
<xs:element name="Framework" minOccurs="0" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Framework characterizes the target using an enumerated list of supported frameworks in which this attack pattern is possible and relevant. USAGE: This element is represented as an enumerated list to facilitate normalization and classification of attack patterns</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="J2EE"/>
<xs:enumeration value=".NET"/>
<xs:enumeration value="Struts"/>
<xs:enumeration value="Spring"/>
<xs:enumeration value="Hibernate"/>
<xs:enumeration value="Other"/>
<xs:enumeration value="All"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
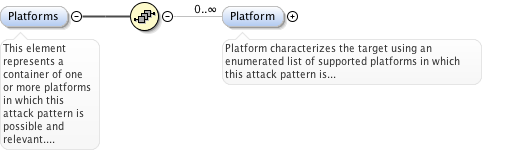
<xs:element name="Platforms" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more platforms in which this attack pattern is possible and relevant. Platforms characterizes the target using an enumerated list of platforms utilized by the target.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
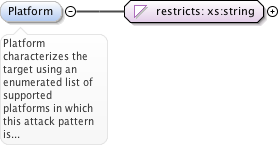
<xs:element name="Platform" minOccurs="0" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Platform characterizes the target using an enumerated list of supported platforms in which this attack pattern is possible and relevant. USAGE: This element is represented as an enumerated list to facilitate normalization and classification of attack patterns</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Windows"/>
<xs:enumeration value="UNIX-LINUX"/>
<xs:enumeration value="Solaris"/>
<xs:enumeration value="Other"/>
<xs:enumeration value="All"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
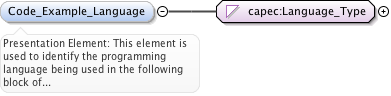
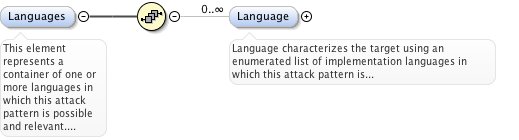
<xs:element name="Languages" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more languages in which this attack pattern is possible and relevant. Languages characterizes the target using an enumerated list of languages utilized by the target.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
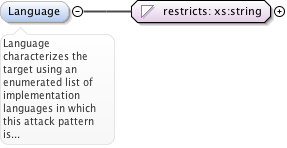
<xs:element name="Language" minOccurs="0" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Language characterizes the target using an enumerated list of implementation languages in which this attack pattern is possible and relevant. USAGE: This element is represented as an enumerated list to facilitate normalization and classification of attack patterns</xs:documentation>
</xs:annotation>
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="AJAX"/>
<xs:enumeration value="ASP"/>
<xs:enumeration value="ASP.NET"/>
<xs:enumeration value="C"/>
<xs:enumeration value="C++"/>
<xs:enumeration value="C#"/>
<xs:enumeration value="Java"/>
<xs:enumeration value="JSP"/>
<xs:enumeration value="PHP"/>
<xs:enumeration value="PERL"/>
<xs:enumeration value="Ruby"/>
<xs:enumeration value="Visual Basic"/>
<xs:enumeration value="Other"/>
<xs:enumeration value="All"/>
</xs:restriction>
</xs:simpleType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
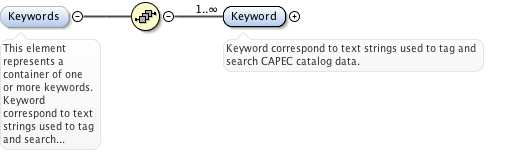
<xs:element name="Keywords" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more keywords. Keyword correspond to text strings used to tag and search CAPEC catalog data.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
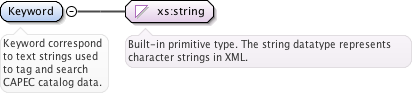
<xs:element name="Keyword" type="xs:string" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Keyword correspond to text strings used to tag and search CAPEC catalog data.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
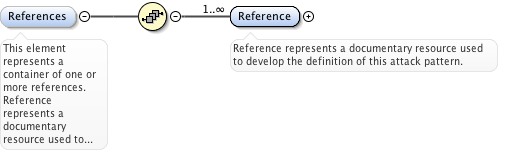
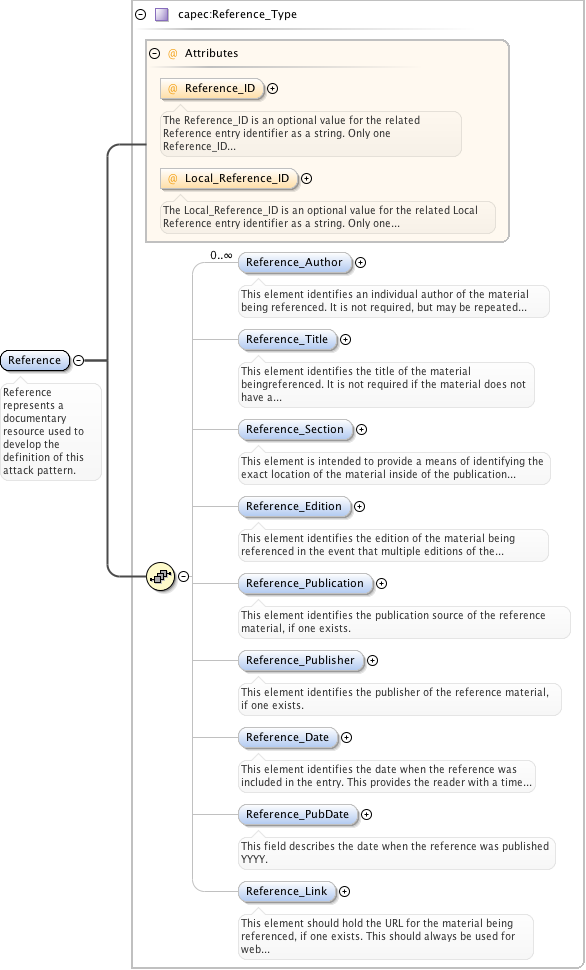
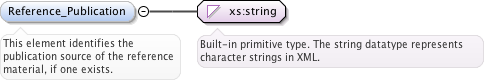
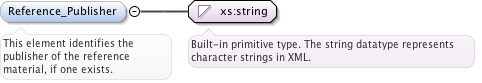
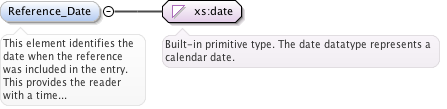
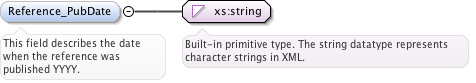
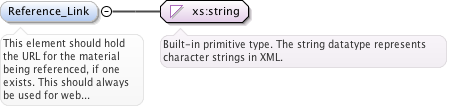
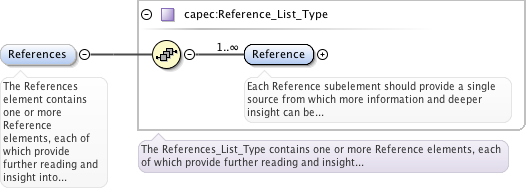
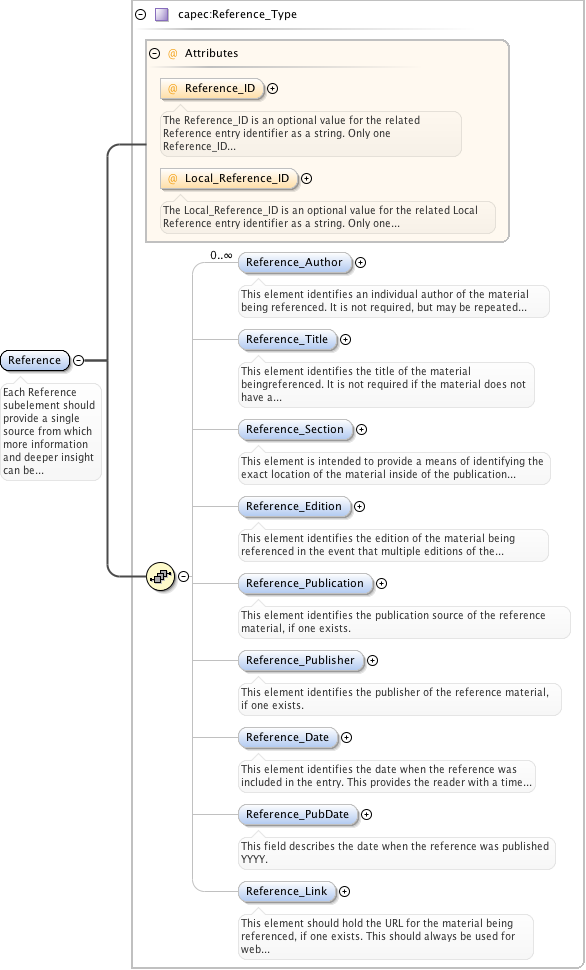
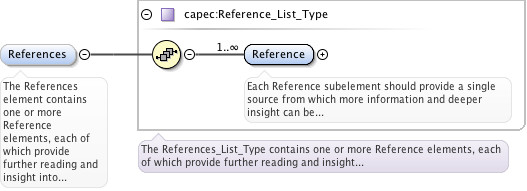
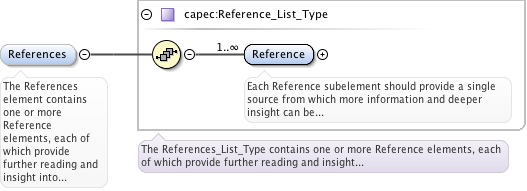
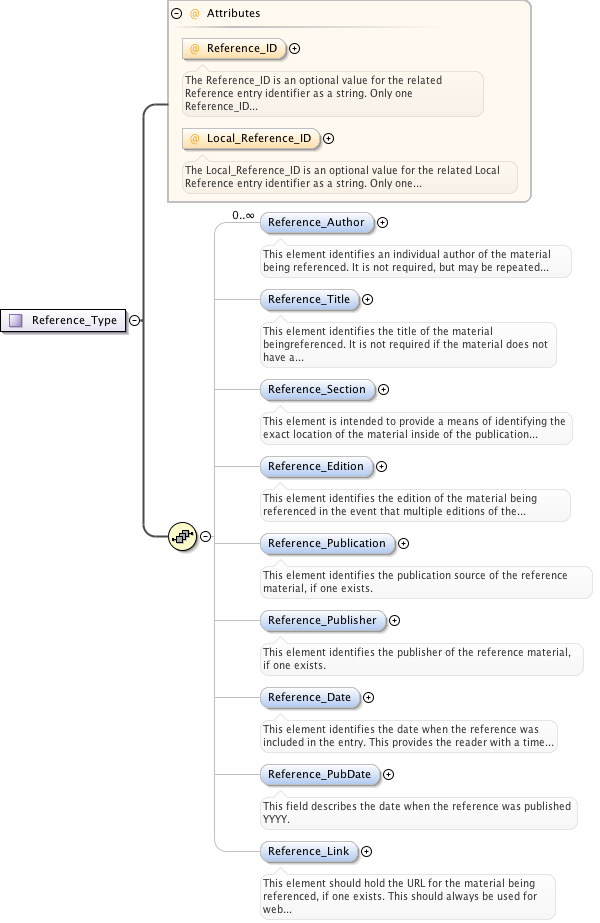
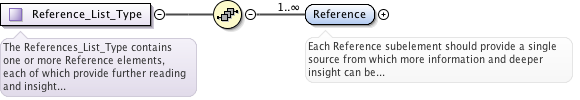
<xs:element name="References" minOccurs="0">
<xs:annotation>
<xs:documentation>This element represents a container of one or more references. Reference represents a documentary resource used to develop the definition of this attack pattern.</xs:documentation>
</xs:annotation>
<xs:complexType>
<xs:sequence>
<xs:element name="Reference" type="capec:Reference_Type" maxOccurs="unbounded">
<xs:annotation>
<xs:documentation>Reference represents a documentary resource used to develop the definition of this attack pattern.</xs:documentation>
</xs:annotation>
</xs:element>
</xs:sequence>
</xs:complexType>
</xs:element>
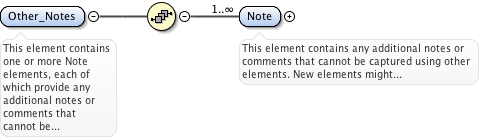
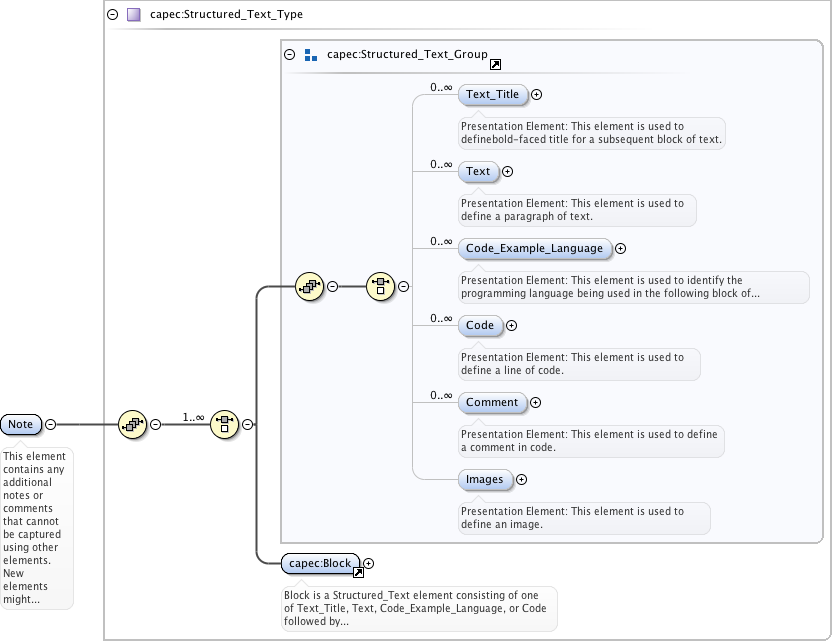
<xs:element ref="capec:Other_Notes" minOccurs="0"/>
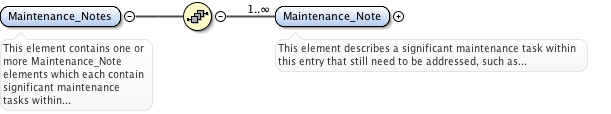
<xs:element ref="capec:Maintenance_Notes" minOccurs="0"/>
<xs:element ref="capec:Content_History" minOccurs="0"/>
</xs:sequence>
<xs:attribute name="ID" type="xs:integer" use="optional" default="0"/>
<xs:attribute name="Name" type="xs:string" use="required"/>
<xs:attribute name="Pattern_Completeness">
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Complete"/>
<xs:enumeration value="Stub"/>
<xs:enumeration value="Hook"/>
</xs:restriction>
</xs:simpleType>
</xs:attribute>
<xs:attribute name="Pattern_Abstraction" use="optional">
<xs:simpleType>
<xs:restriction base="xs:string">
<xs:whiteSpace value="collapse"/>
<xs:enumeration value="Meta"/>
<xs:enumeration value="Standard"/>
<xs:enumeration value="Detailed"/>
</xs:restriction>
</xs:simpleType>
</xs:attribute>
<xs:attribute name="Status" type="capec:Status_Type" use="required">
<xs:annotation>
<xs:documentation>The Status attribute defines the status level for this view.</xs:documentation>
</xs:annotation>
</xs:attribute>
</xs:complexType> |